Hash Generator
Generate MD5, SHA-1, SHA-256, and SHA-512 hashes from text or any file. All four hashes are computed at once. Runs entirely in your browser — your data never leaves your device.
Which algorithm to use?
SHA-256 is the modern default — used in TLS certificates, code signing, and most security protocols. SHA-512 provides a larger output (512 bits vs 256) for extra margin. SHA-1 is deprecated for security use but still common in Git object IDs. MD5 is broken for cryptographic purposes but widely used for fast file integrity checks and non-security checksums.
File integrity verification
Download a file, then hash it and compare to the SHA-256 or MD5 checksum published by the software vendor. If the hashes match, the file was not tampered with in transit. This is how Linux ISO downloads, npm packages, and Docker images are verified before use.
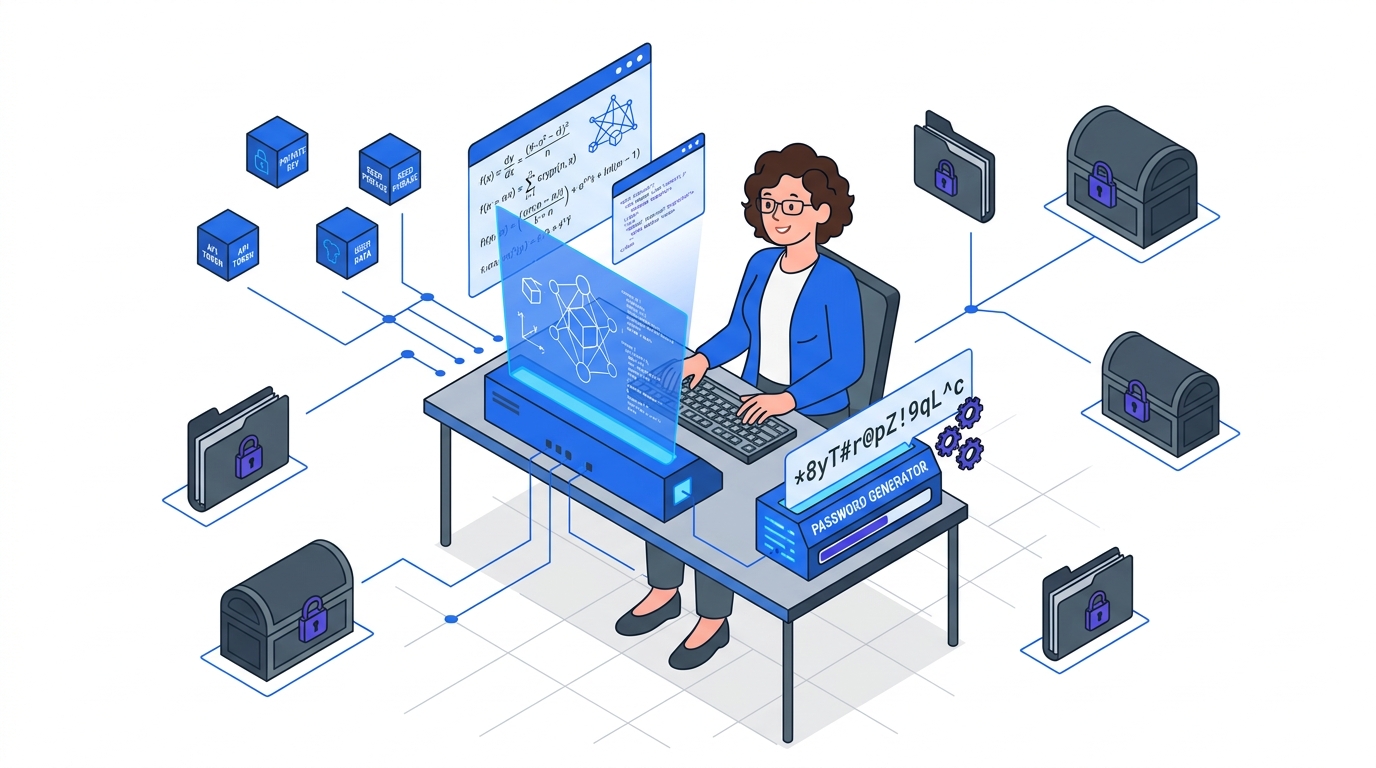
Are these secure for passwords?
No. MD5, SHA-1, SHA-256, and SHA-512 are all fast hash functions, which makes them unsuitable for password storage. Password hashing requires slow, memory-hard algorithms: bcrypt, scrypt, or Argon2. Fast hashes can be brute-forced at billions of attempts per second on a GPU.