Business-IT Insights
Strategic technology insights for business leaders and CTOs.
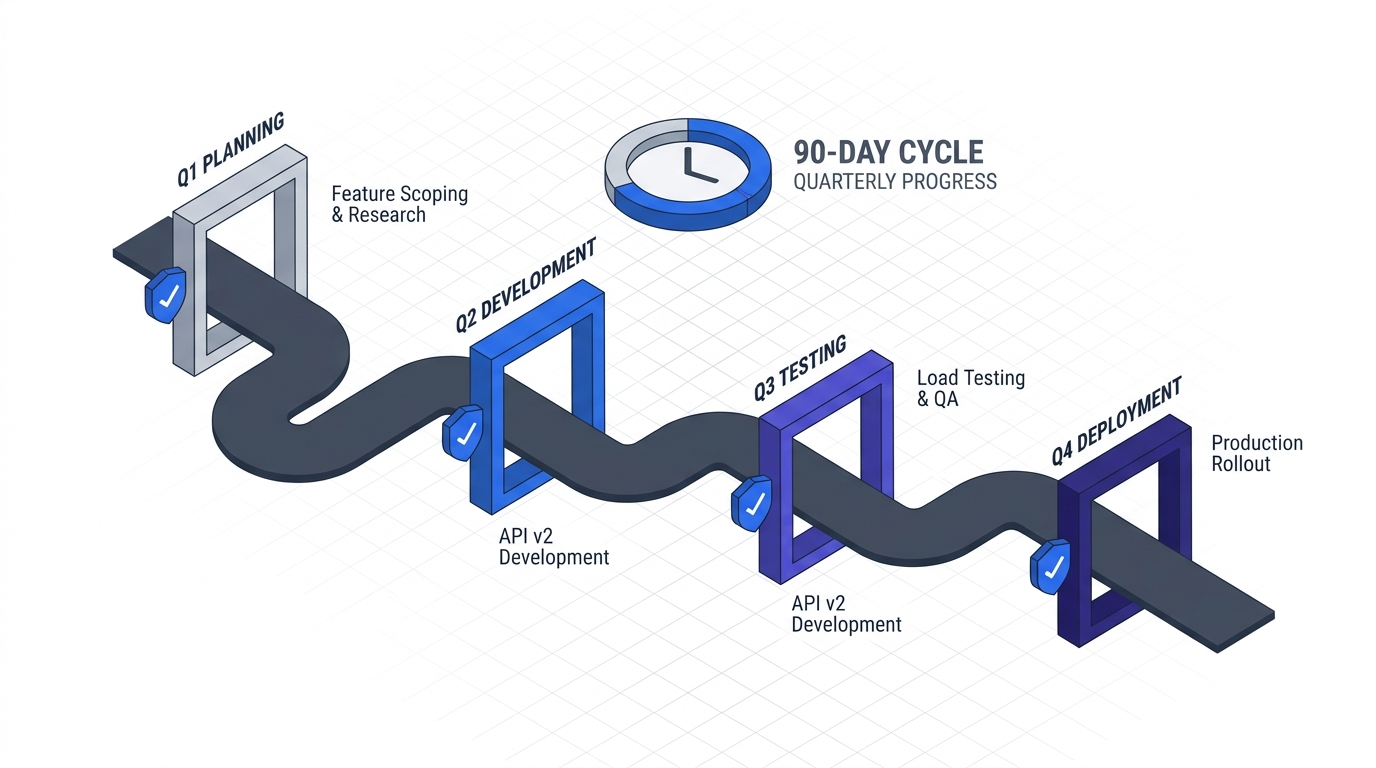
The 90-Day Zero Trust Adoption Playbook
63% of organizations started Zero Trust — but only 10% reach maturity. This phase-gated playbook delivers the operational sequencing, decision frameworks, and brownfield-honest guidance that vendor docs and CISA abstractions leave out.
Open the playbook →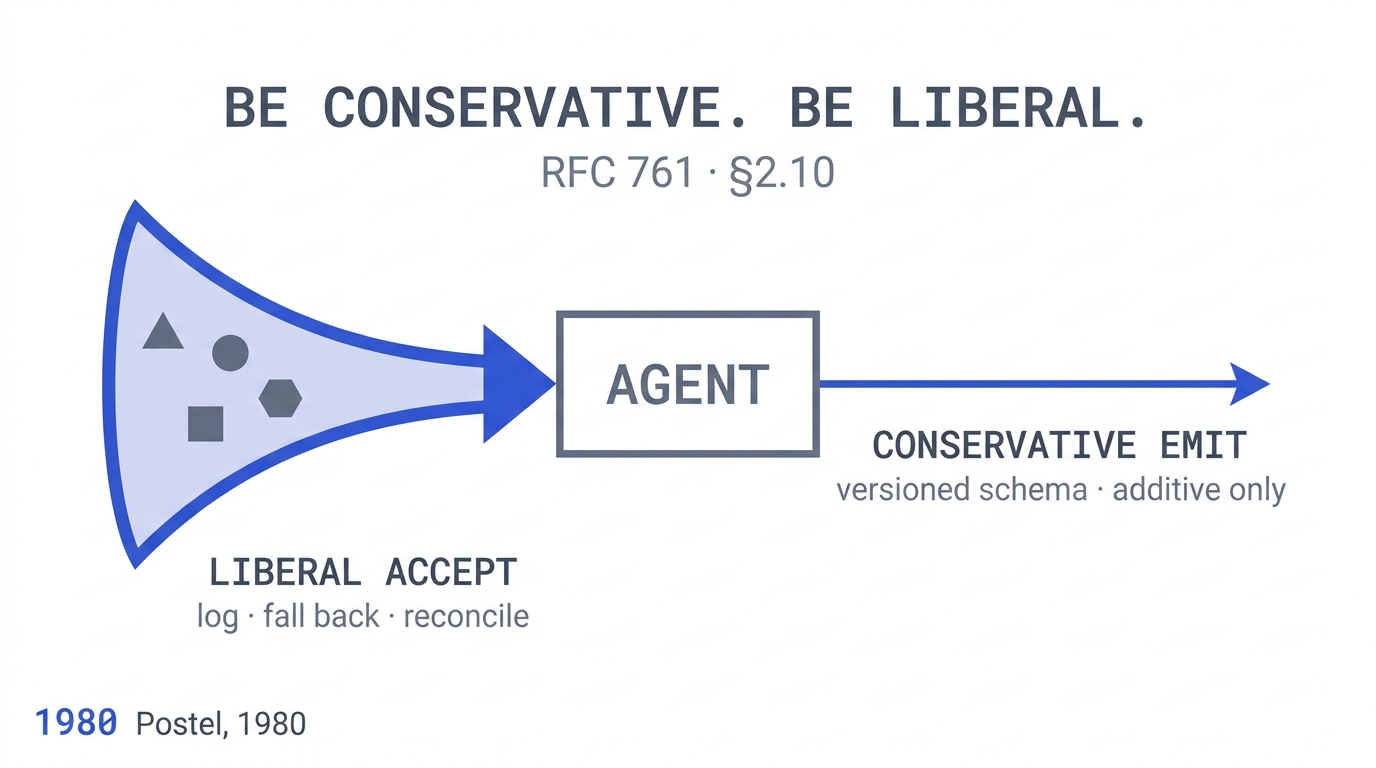
Postel's Law and Why Your AI Agents Fight Each Other
Multi-agent LLM systems fail 41–86.7% of the time across 7 frameworks. A 45-year-old protocol-design rule explains why — and what to do about it.
Read article →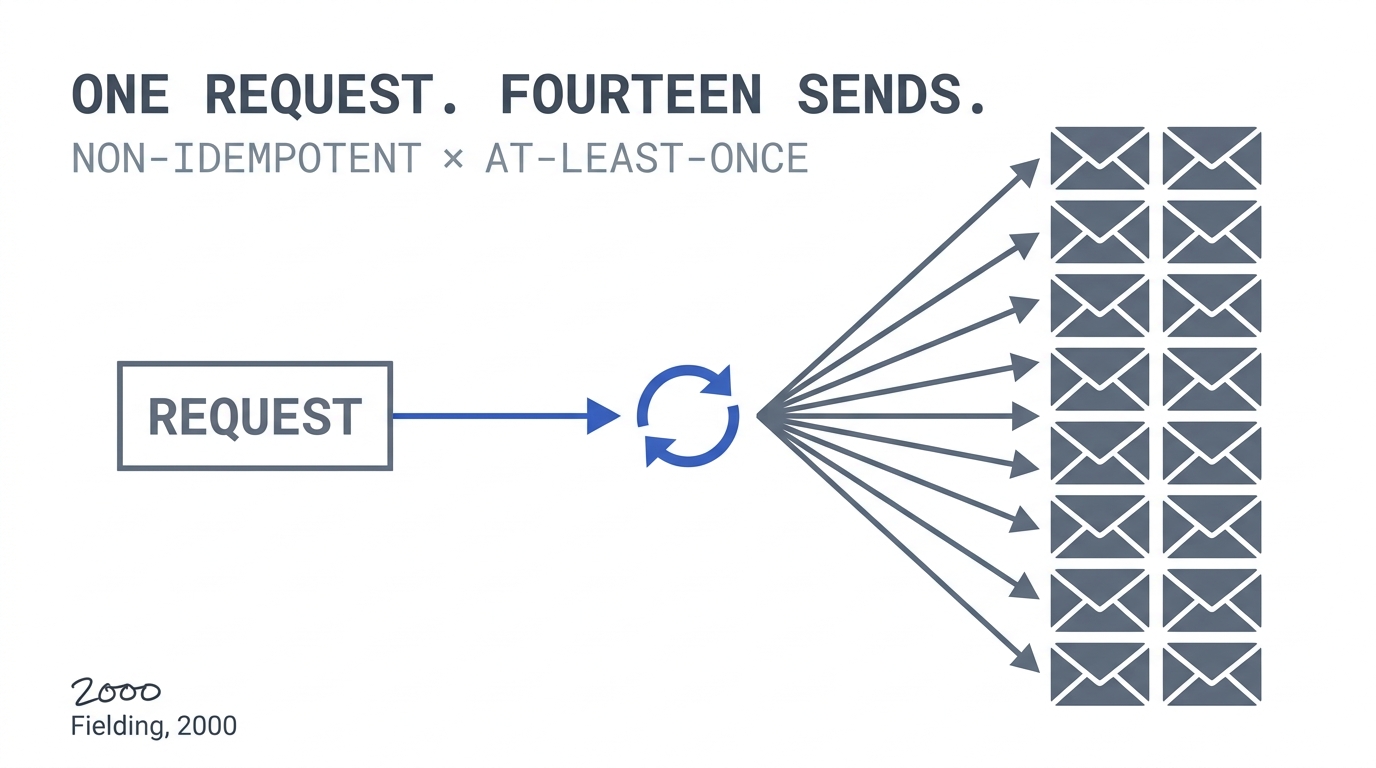
Why Every AI Agent Failure I've Debugged in 2026 Was an Idempotency Problem
Five real production failures, the 25-year-old constraint that explains them, and the architectural fix every agent platform team should have shipped last quarter.
Read article →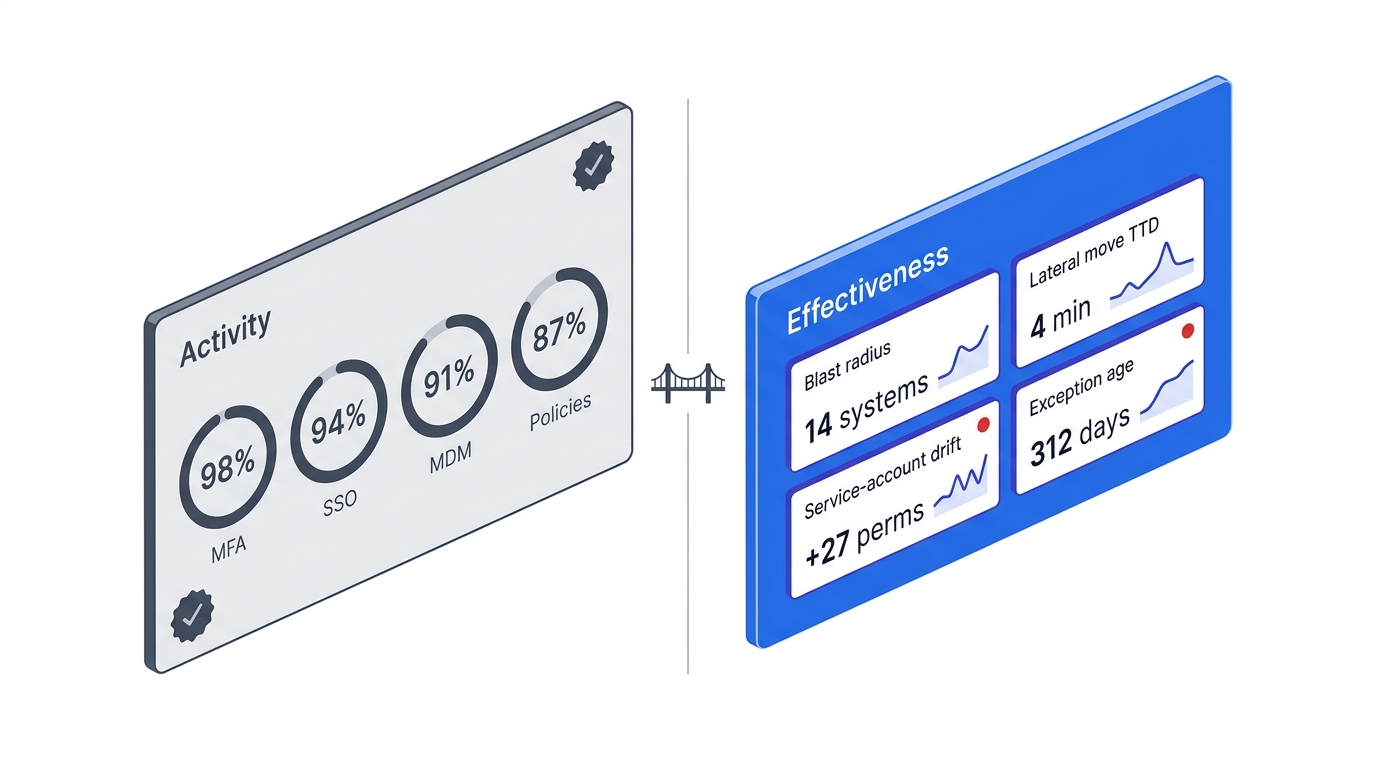
How to Compute Zero Trust Effectiveness: Four Metrics That Survive a Breach
MFA coverage and SSO percentages are activity metrics — they go up whether or not your blast radius shrinks. The four metrics that prove Zero Trust is working: blast radius, lateral-movement time-to-detect, service-account scope drift, and exception age. With concrete queries for SIEM, IAM, and Kubernetes.
Read article →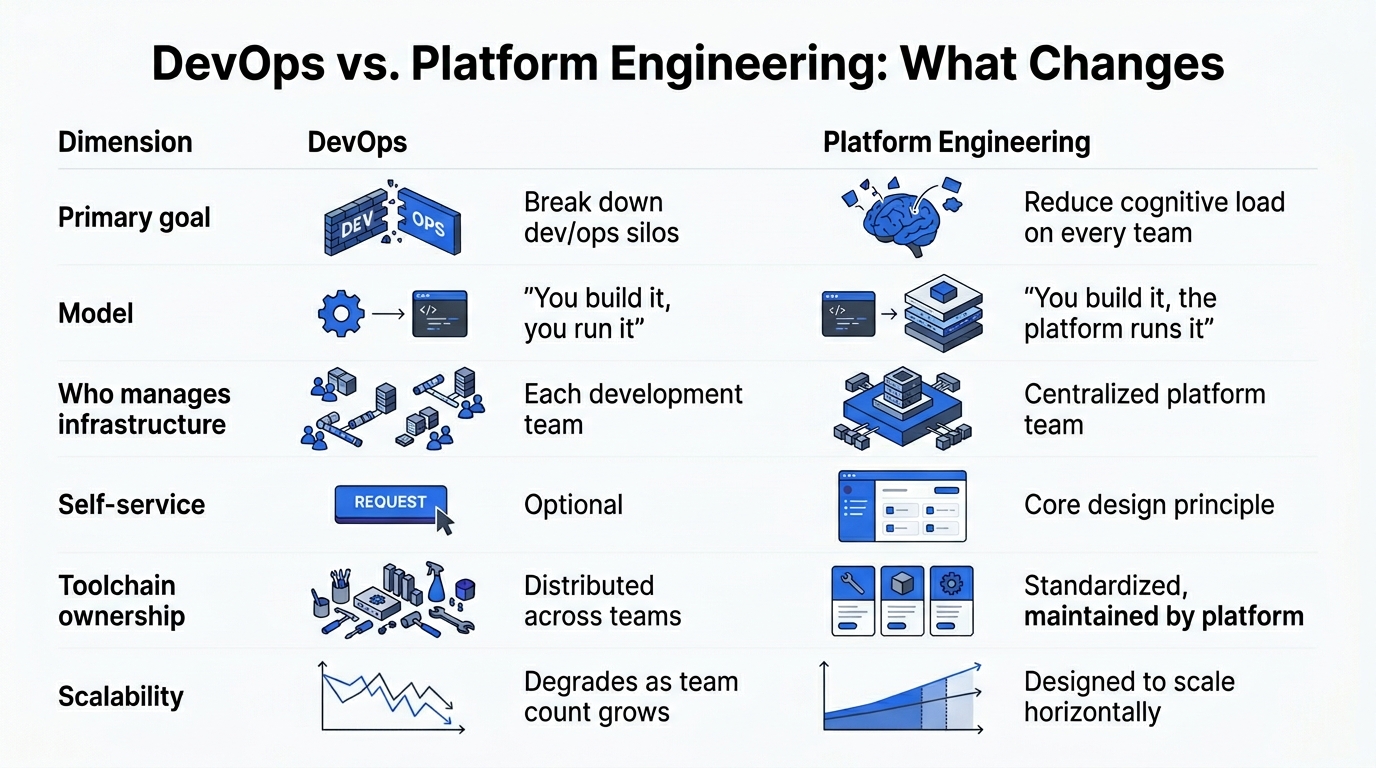
How to Measure Voluntary Adoption of Your Internal Developer Platform
Activity metrics like deploys and onboarded services hide whether developers actually want your platform. Three concrete measurements — path-of-least-resistance rate, stickiness, and re-entry — that prove an IDP is earning adoption instead of forcing it.
Read article →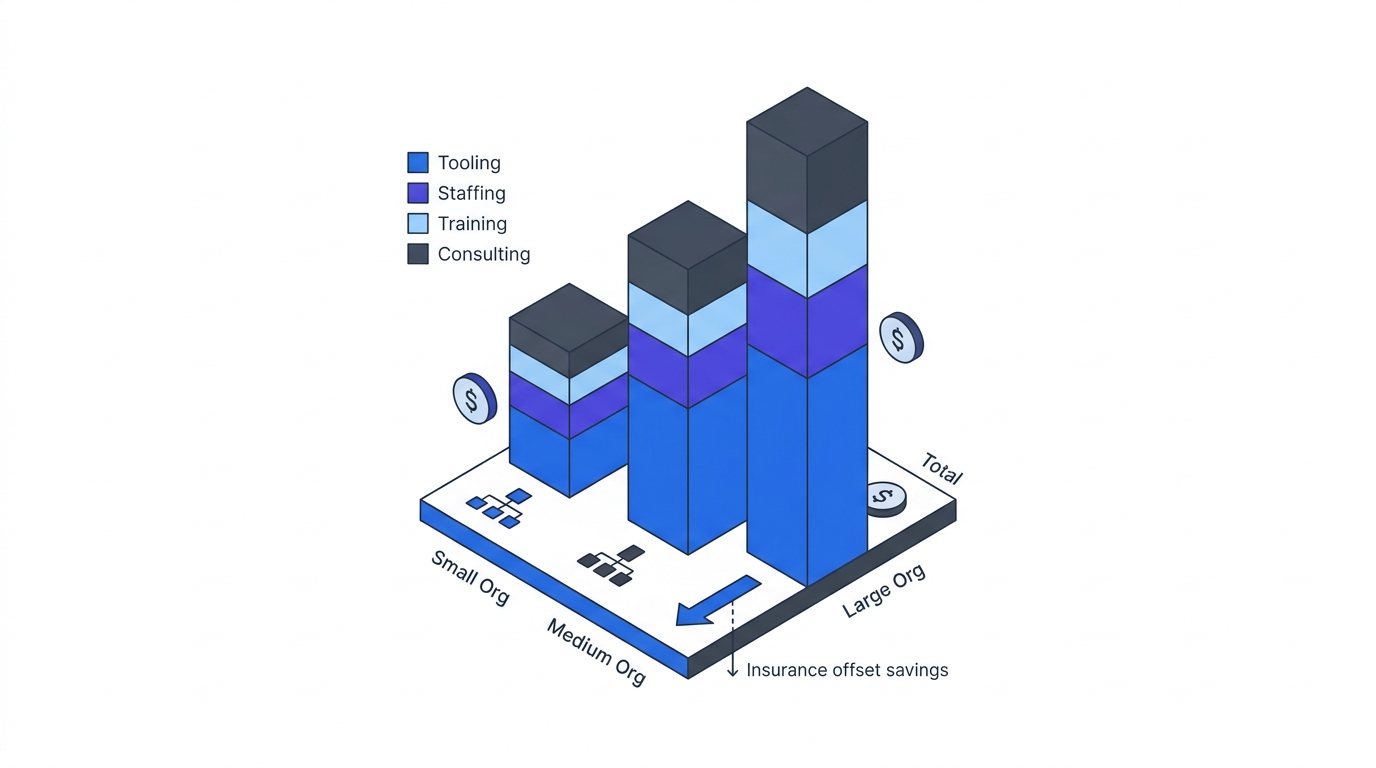
Zero Trust Budgeting: What It Actually Costs
The vendor pricing table nobody publishes. Staffing cost by org size. The skills gap reality. The insurance offset. Here's the honest budget for a 90-day Zero Trust foundation and the Year-Two expansion — with the numbers, not the hand-waving.
Read article →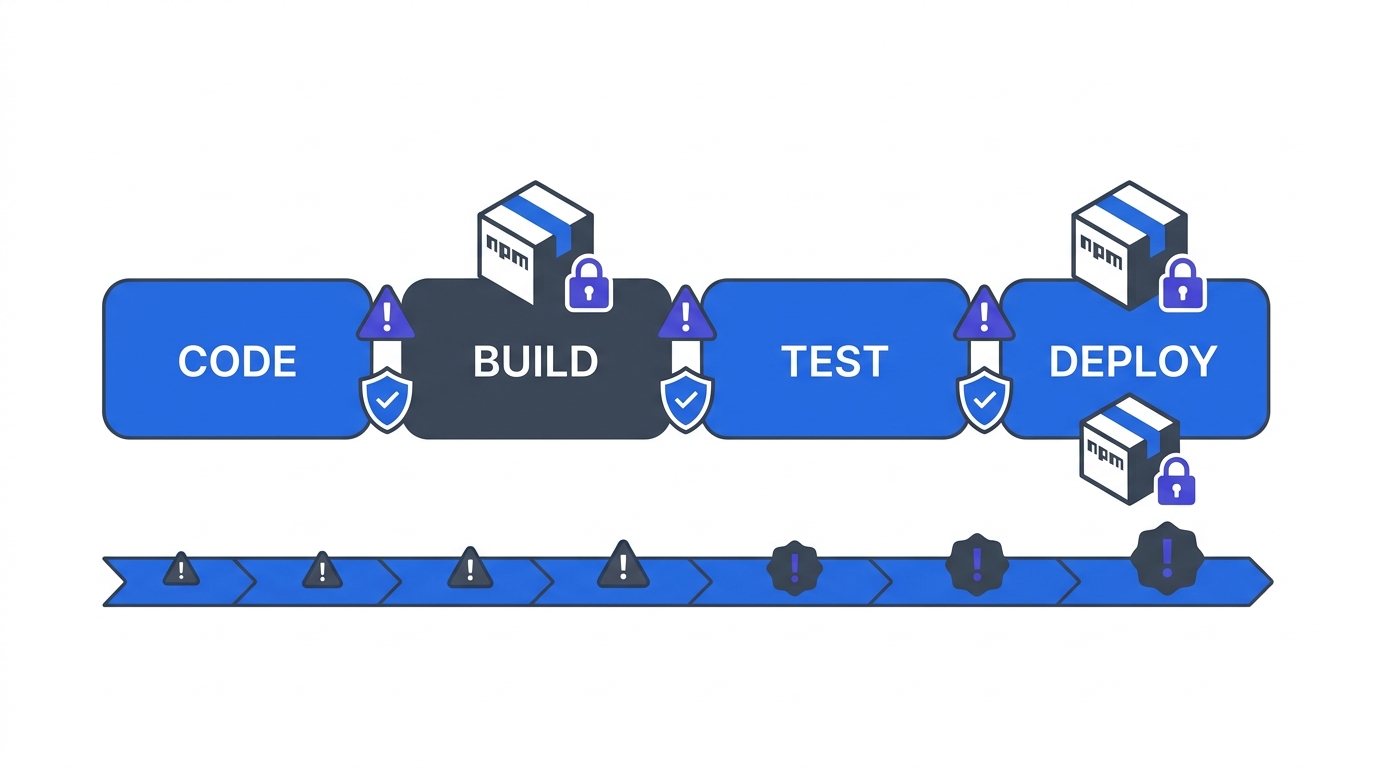
CI/CD Pipeline Hardening: Lessons from the Axios Compromise
The March 2026 axios compromise weaponised a pipeline with static npm credentials and no provenance. Here are the four controls — OIDC federation, per-job secrets, dependency verification, egress restriction — that make your CI/CD a Zero Trust asset instead of a Zero Trust blast radius.
Read article →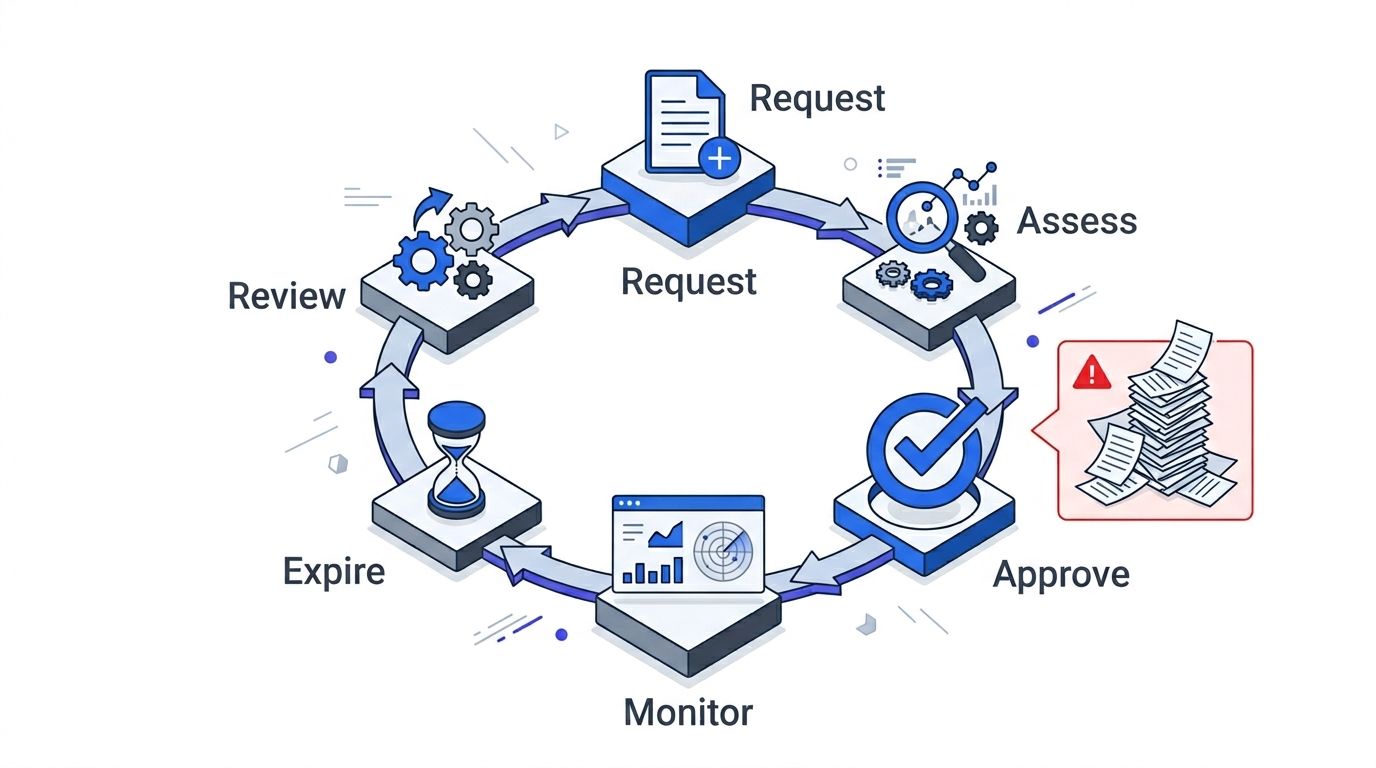
Exception Management: The Framework Every Other Playbook Ignores
Zero Trust is a trust-by-exception model. Without a formal lifecycle, exceptions become permanent bypasses and the programme silently erodes. Here's the six-step framework — request, assess, approve, monitor, expire, review — with the anti-patterns it prevents.
Read article →
Graduated Enforcement: From Monitor to Hard Enforce Without Breaking Production
The anti-pattern is flipping enforcement on everywhere at once, breaking production, and retreating to permissive. Here's the five-step graduation sequence, rollback triggers, and canary strategy that ship segmentation without taking down revenue.
Read article →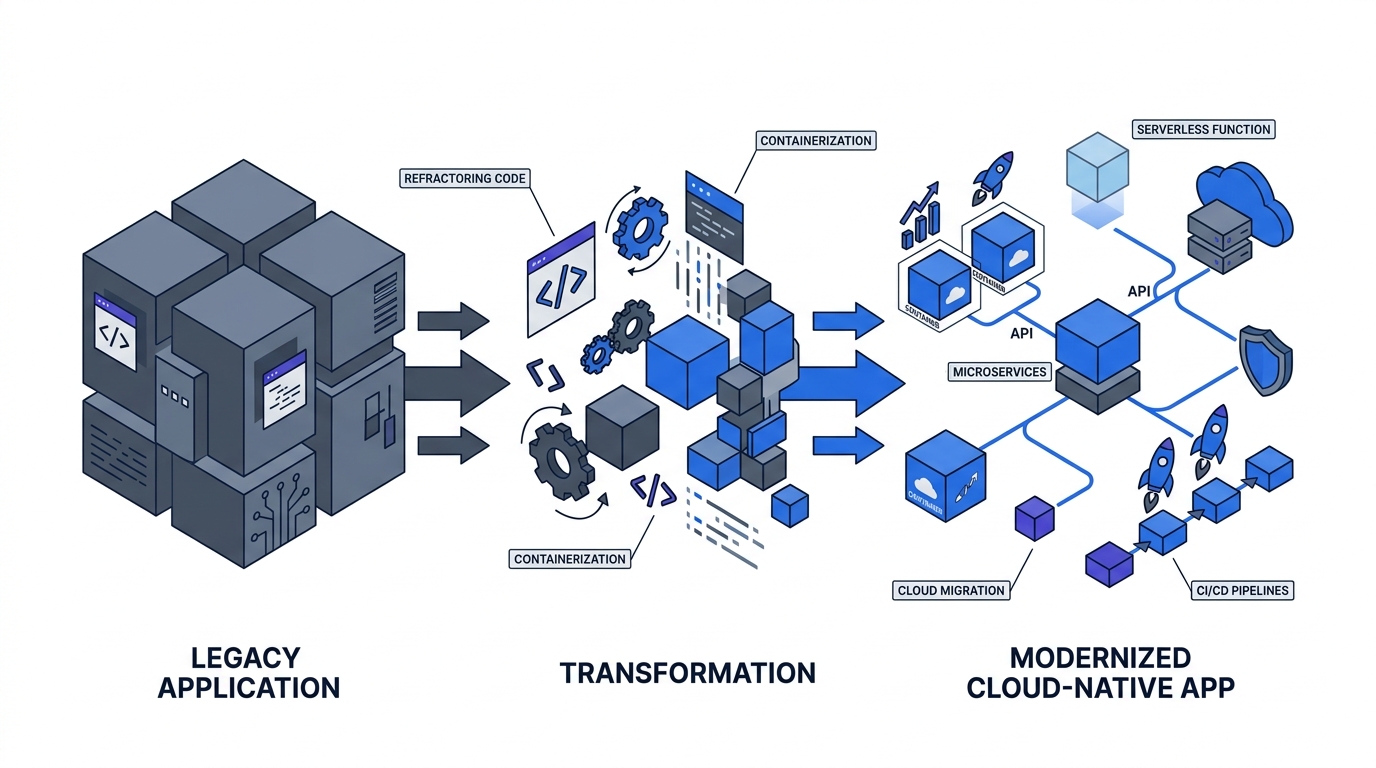
The Legacy System Playbook: Four Strategies for Apps That Can't Do Zero Trust
70% of enterprises maintain legacy apps for 10+ years. You won't retrofit Zero Trust into a 1998 mainframe. Here are the four strategies — wrap, isolate, sidecar, replace — and the decision logic for picking the right one per system.
Read article →
Measuring Zero Trust: The Dashboard Your Board Wants to See
70% of boards now review cybersecurity quarterly. They want financial exposure, not firewall logs. Here are the leading and lagging indicators, the CISA maturity scoring overlay, and the dollar-denominated framing that gets Zero Trust funded past year one.
Read article →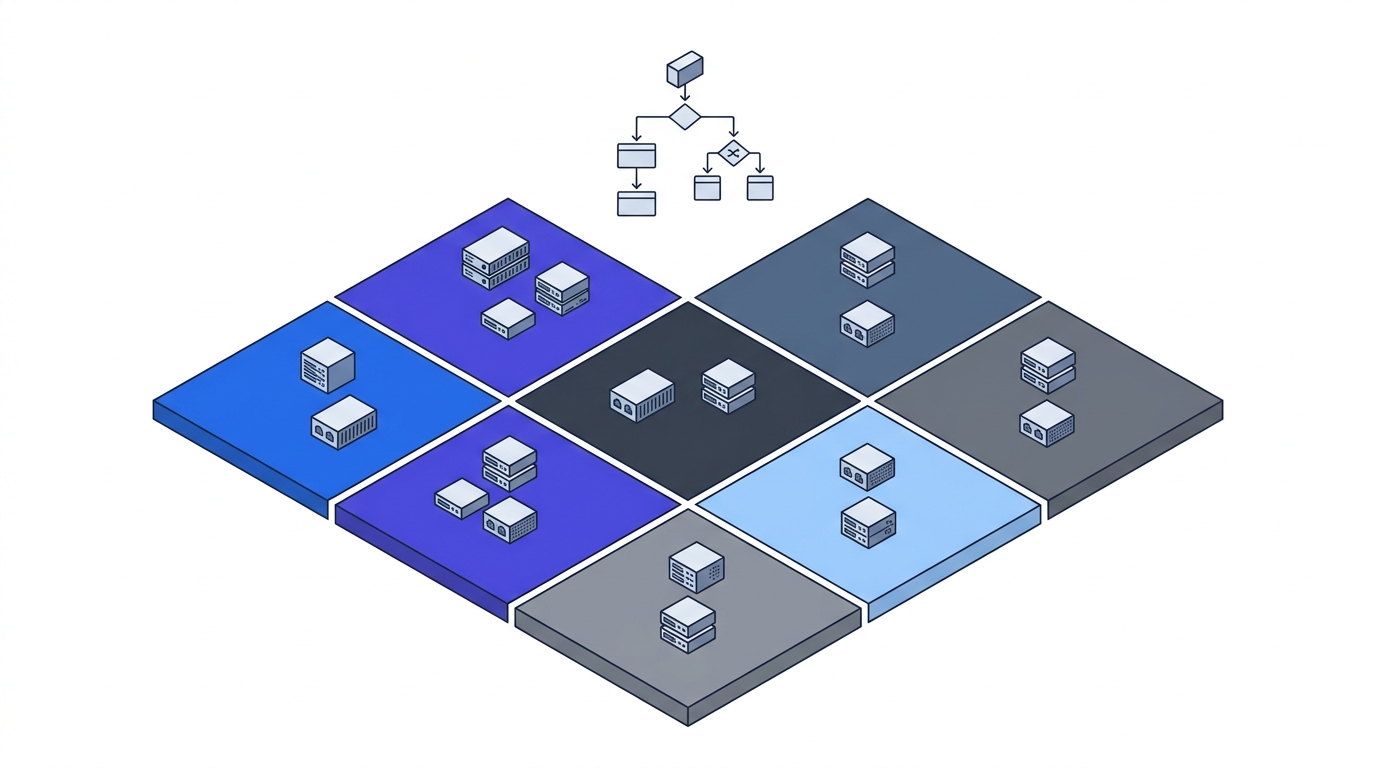
Micro-Segmentation Design: Choosing Your Approach
Design comes before enforcement. Here's the environment-first decision tree for picking a micro-segmentation approach — host-based, service mesh, eBPF, cloud-native — without locking yourself into the wrong tool.
Read article →
Device Trust & BYOD: The Access Matrix Every CTO Needs
82–95% of enterprises allow BYOD, but 80–90% of ransomware lands on unmanaged devices. Here's the four-tier access matrix that lets you say yes to BYOD without saying yes to compromise.
Read article →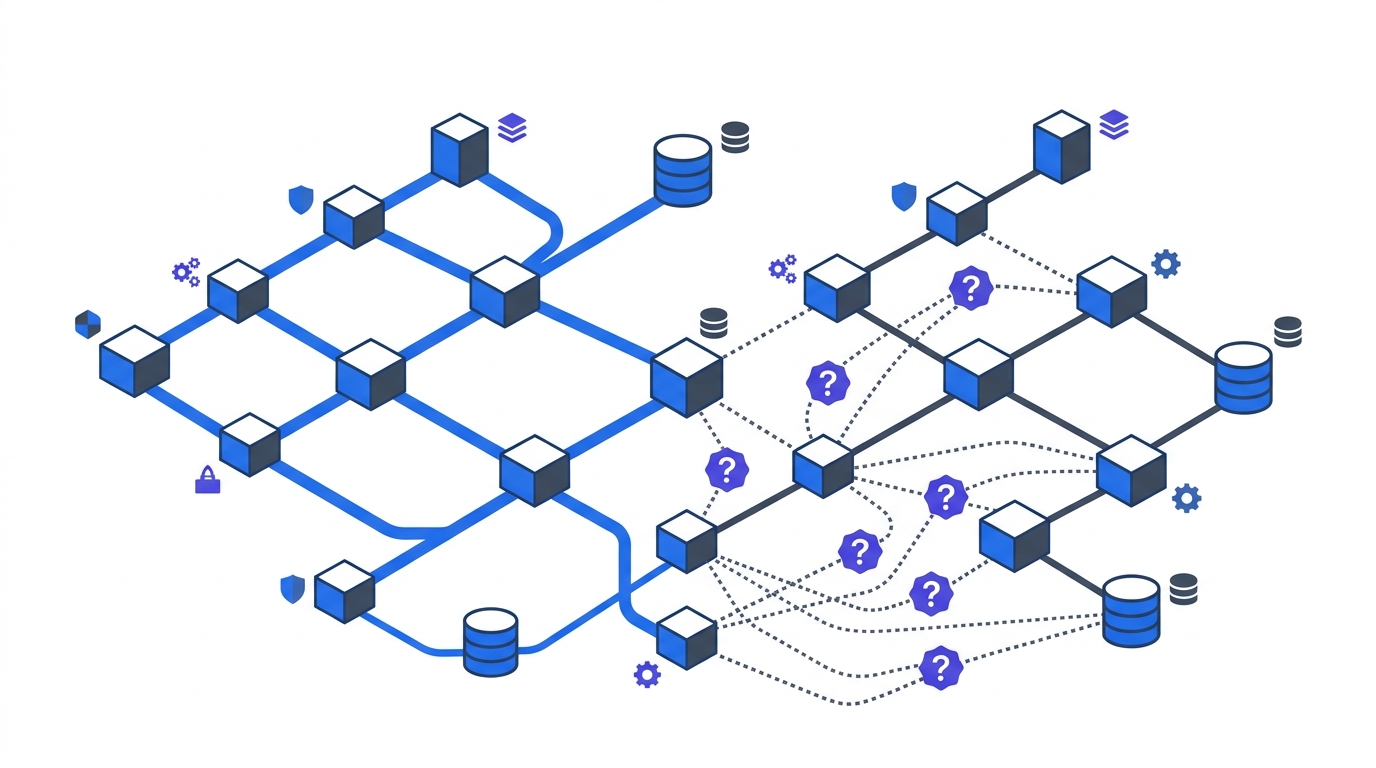
Network Baselining: What You'll Discover (and Why It Matters)
You cannot segment what you cannot see. Most enterprises underestimate their cloud app footprint by 30x. Here's the baselining playbook that turns flow data into a segmentation blueprint.
Read article →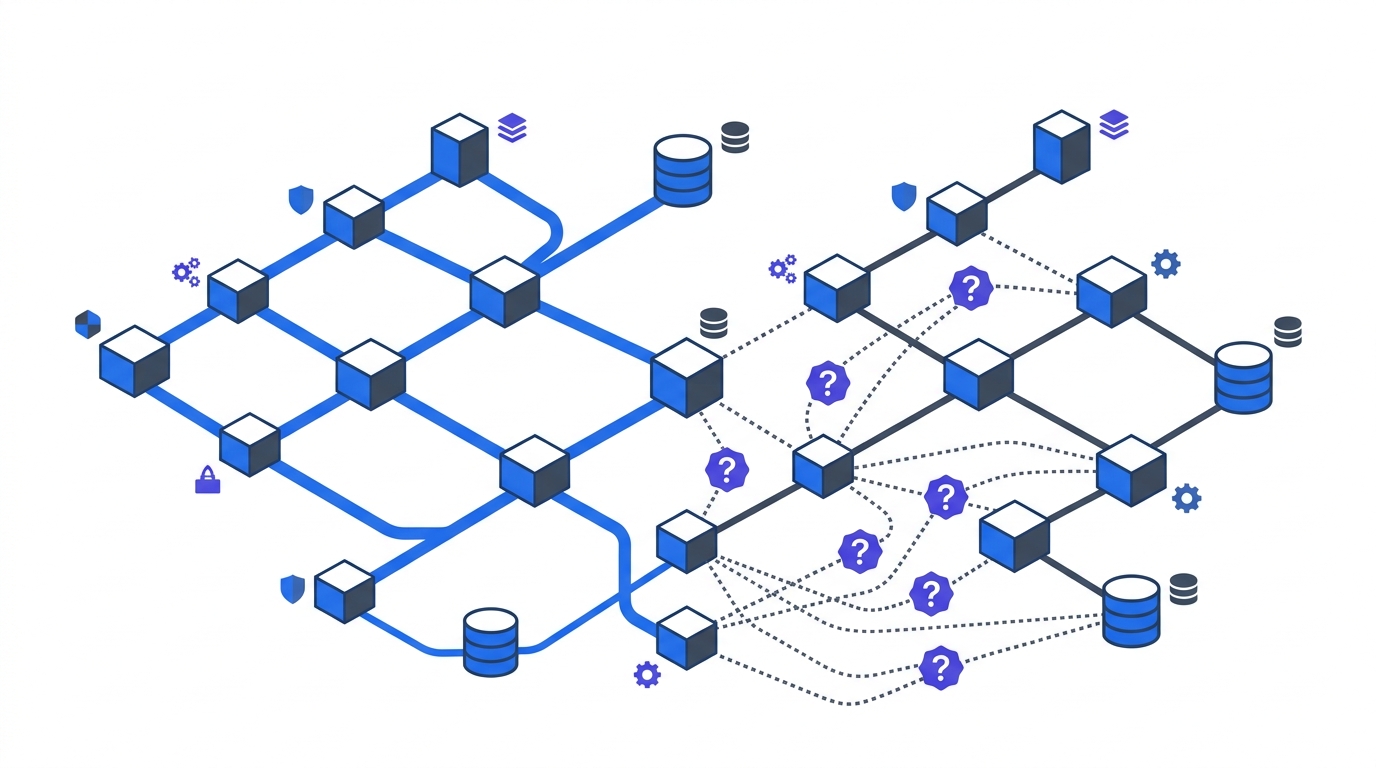
Conditional Access: What Shadow Mode Will Reveal Before You Enforce
Never enforce Conditional Access on Day 1. Here's what two weeks of report-only mode reveal, from 1,000+ shadow IT apps to legacy auth to VIP non-compliance.
Read article →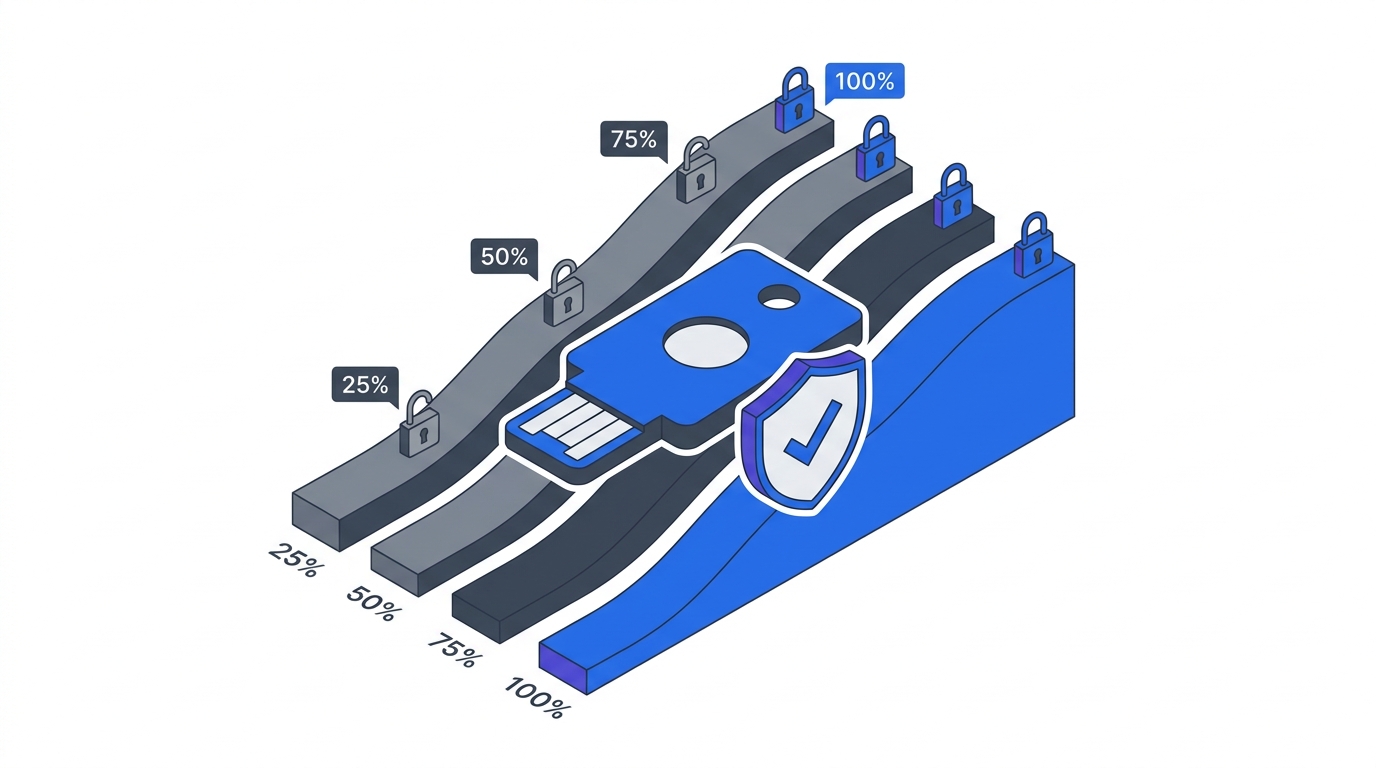
MFA & SSO Rollout: The Realistic Timeline for Enterprise Zero Trust
Enterprise MFA and SSO rollouts take 3-6 months, not 3 weeks. Here's the phased timeline, helpdesk reality, and legacy-auth decision tree that keep Phase 1 on track.
Read article →
The Service Account Crisis: Triage Your 82:1 Machine Identity Ratio
Enterprises now run 82 machine identities per employee. Here's the triage framework for service accounts, orphaned credentials, and the migration path to dynamic secrets.
Read article →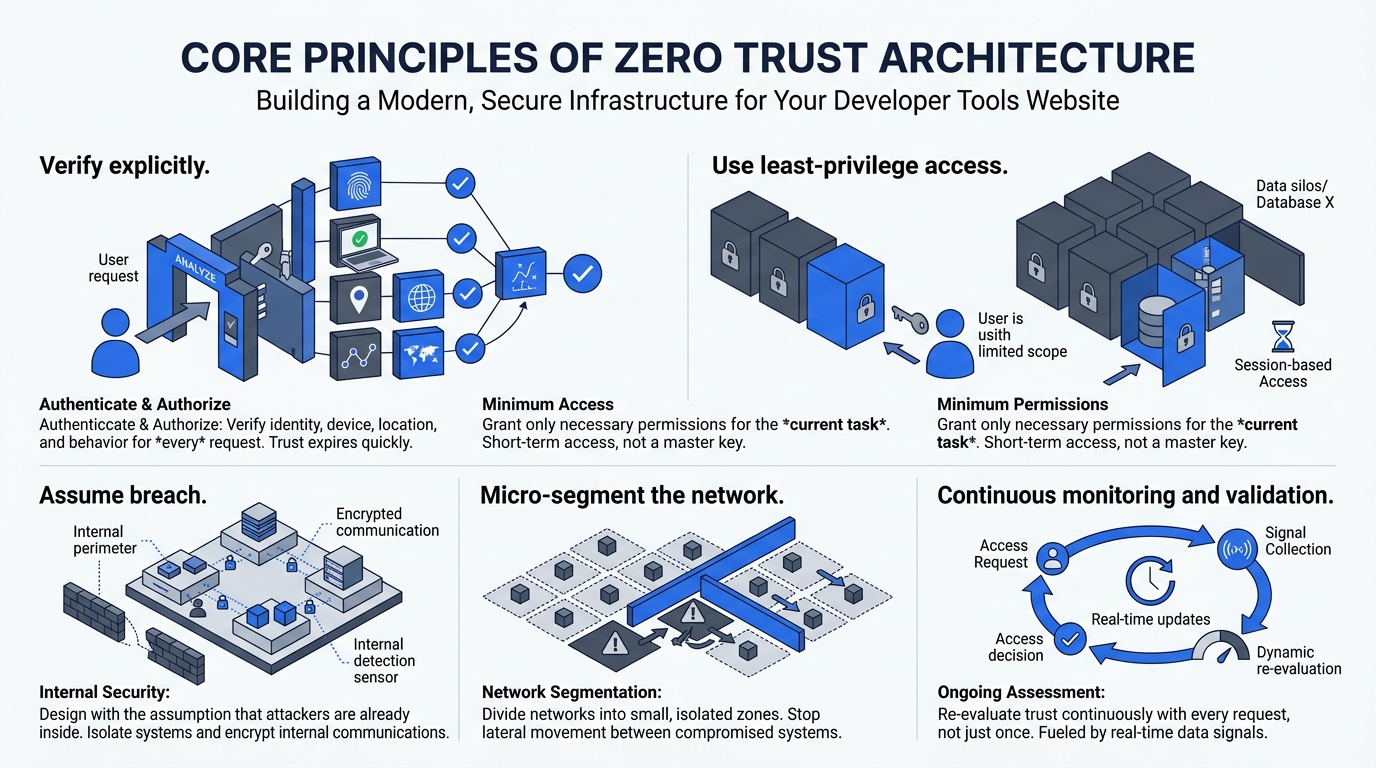
The Axios npm Compromise: Why Zero Trust Is a Blast-Radius Control, Not a Prevention Control
On 31 March 2026, two compromised axios releases briefly distributed a cross-platform RAT via npm. A CTO and architect case study on what Zero Trust Architecture actually contains — and what it does not.
Read article →
The Application Criticality Scorecard: Prioritizing Your Zero Trust Rollout
Scope creep is the #1 Zero Trust failure mode. This three-axis scoring model helps CTOs prioritize which applications to secure first — with worked examples and inventory timelines.
Read article →
Zero Trust Baseline Metrics: Your 'Before' Snapshot
You can't show Zero Trust progress without a starting point. Here are the metrics to capture before Day 1 — with industry benchmarks so you know where you stand.
Read article →
Building Your Zero Trust Governance Structure
The hardest Zero Trust challenges are organizational, not technical. 88% of CISOs face significant implementation challenges — here's the governance framework that keeps programs from stalling.
Read article →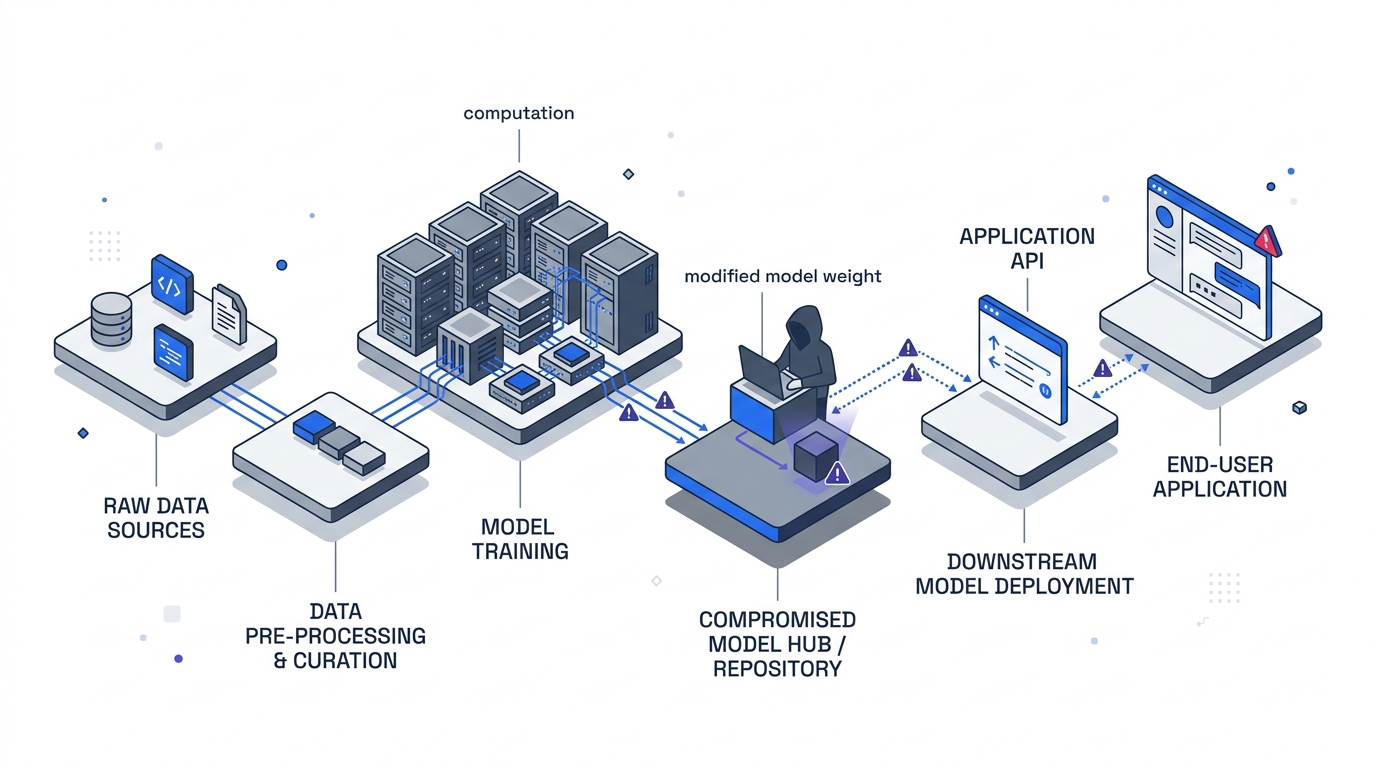
Your Agent Is Mine: What 428 LLM API Routers Reveal About the Next Supply-Chain Attack Surface
A UCSB-led study of 428 commodity LLM API routers found 9 actively injecting malicious code and 401 of 440 autonomous coding sessions running in auto-approve mode. A CTO and architect read of the paper — with the caveats stated plainly.
Read article →
Application Modernization
Application Modernization: The Executive Guide for 2026
Legacy systems consume 60–80% of IT budgets (Gartner), starving innovation. What executives need to understand about application modernization strategy in 2026.
Application Modernization: The Business Case Every CFO and CTO Must Make in 2026
228% ROI in 3 years, 80% of IT budgets locked in legacy, DORA director liability exposure. The application modernization business case with hard data.
Application Modernization: Technology Deep Dive for Enterprise Architects
The 6Rs, Strangler Fig vs. big-bang rewrites, mTLS, and how to sequence a modernization programme without breaking production. A practitioner's guide for 2026.

Platform Engineering
Platform Engineering: The Executive Guide for 2026
What is platform engineering, why Gartner predicts 80% adoption by 2026, and how internal developer platforms (IDPs) eliminate friction and transform delivery.
Platform Engineering: The Business Case Every CTO Must Make in 2026
224% ROI, $4.41M NPV, 6-month payback — the Forrester data behind platform engineering investment, plus PESTEL forces, SWOT, and developer attrition costs.
Platform Engineering: Technology Deep Dive for Enterprise Architects
Backstage, Argo CD, Crossplane, and OPA: the IDP reference architecture and implementation patterns for a scalable Internal Developer Platform in 2026.

Zero Trust Architecture
Zero Trust Architecture: The Executive Guide for 2026
63% of organizations started Zero Trust — but only 10% reach maturity by 2026, per Gartner. What every executive needs to know before the mandates hit.
Zero Trust Architecture: The Business Case Every CTO Must Make in 2026
PESTEL analysis, ROI data, and the business case for Zero Trust — $4.88M average breach cost, 111% Forrester ROI, and what NIS2 means for director liability.
Zero Trust Architecture: The Technology Deep Dive for Enterprise Architects
NIST SP 800-207 pillars, micro-segmentation, mTLS, SPIFFE/SPIRE, and the software development changes required to build a Zero Trust-ready organization in 2026.