MFA & SSO Rollout: The Realistic Timeline for Enterprise Zero Trust
Published
Identity is the first Zero Trust pillar for a reason: every other control depends on it. Yet most MFA projects stumble on timeline assumptions. Okta’s deployment methodology places complex enterprise SSO rollouts at 3-6 months, and a 2021 IACIS case study documents a six-phase MFA rollout pattern that still defines the state of the art.
This article is Phase 1 of our 90-Day Zero Trust Playbook. If identity coverage stalls, nothing downstream works. Conditional access has nothing to condition on. Device trust has no user anchor. Micro-segmentation becomes theater. So before you touch networks or devices, you finish identity. That means phishing-resistant MFA for humans, SSO coverage for sanctioned apps, and a legacy-auth plan that is neither magical nor optional.
Key Takeaways
- Complex enterprise SSO rollouts take 3-6 months; MFA rolls out in 20-25% waves over 8-12 weeks (Okta; IACIS, 2021)
- 97% of credential stuffing attacks and 99% of password spray attacks use legacy authentication (Microsoft Learn)
- Disabling legacy auth reduces account compromises by 67% (CYE Security)
- Helpdesk lockout tickets can reach 50% of total volume during rollout, at roughly $87 per password reset (Cisco Duo; F5 Labs)
- Enterprise MFA adoption hits 87% at 10,000+ employee orgs but drops to 34% at small firms (JumpCloud)
Why Does Identity Come First in Zero Trust?
Every CISA pillar beyond Identity, Devices, Networks, Applications, and Data, assumes you can answer “who is this?” with confidence. Microsoft reports 92% of its productivity accounts now use phishing-resistant MFA, and Google’s 2018 rollout of FIDO2 hardware keys to 85,000 employees drove successful phishing attacks to zero.
The logic is uncomfortable but clean: if an attacker owns the identity, device posture and network segmentation become delays, not defenses. CISA designates only FIDO/WebAuthn and PKI-based authentication as “gold standard” phishing-resistant methods. SMS and voice callbacks are on the exit ramp, not the roadmap.
What Does a Realistic MFA Rollout Timeline Look Like?
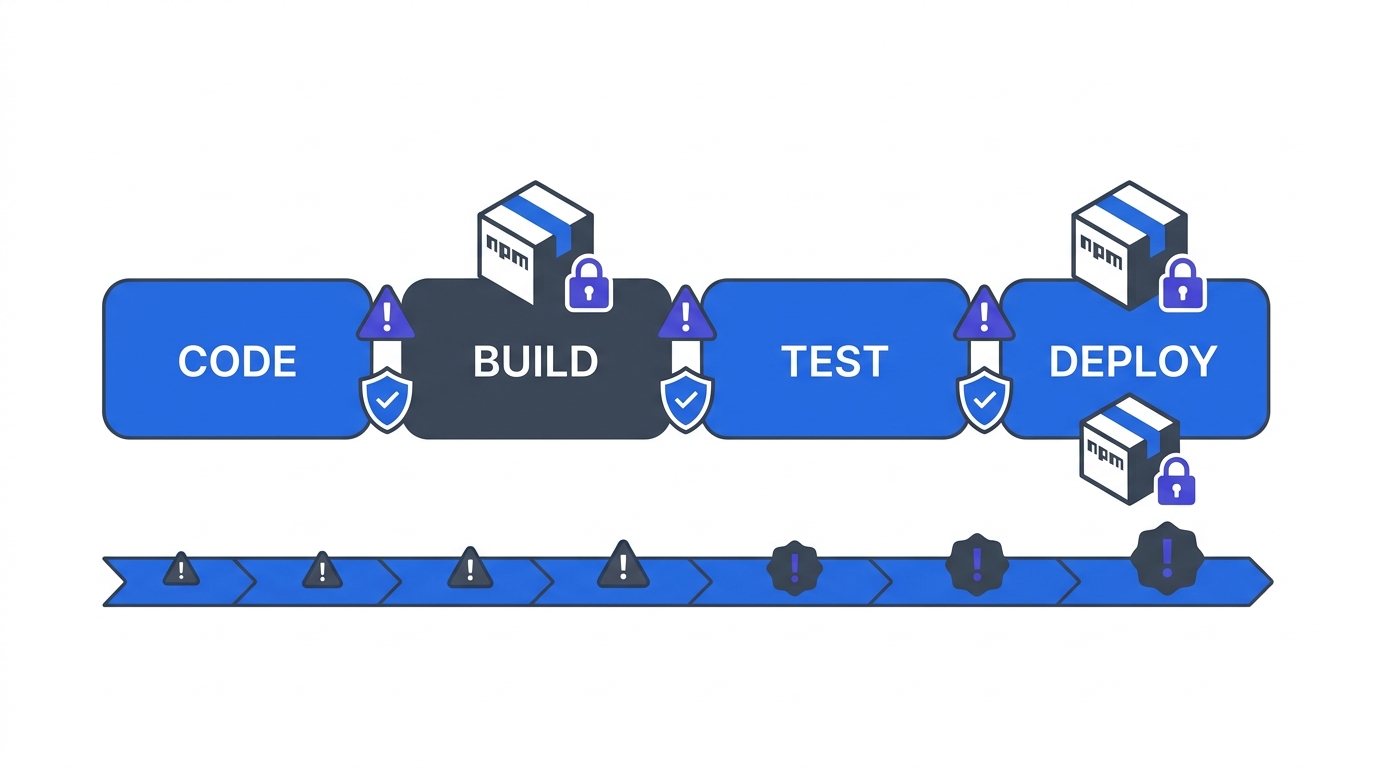
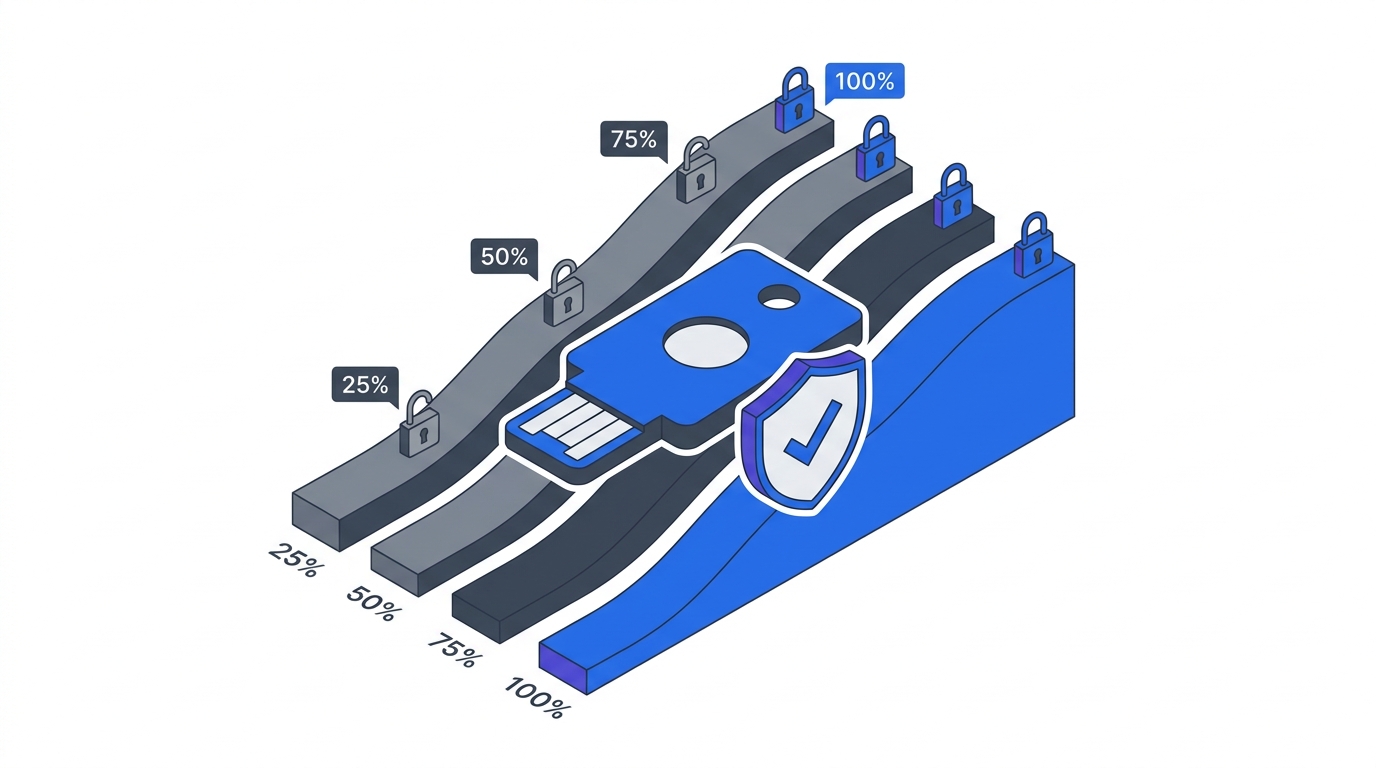
The IACIS 2021 deployment case study describes a pattern that matches what we see in the field: two weeks of pilot planning with helpdesk staff and 200-1,000 early adopters, then four weeks measuring registration and ticket volume, then 20-25% enforcement waves through weeks 7-12. That cadence isn’t slow. It’s survivable.
Here is the sequence that keeps production intact:
- Weeks 1-2: Pilot. Helpdesk staff and volunteer power users enroll first. They become your internal support layer when the broader rollout generates tickets.
- Weeks 3-4: Wave 1 (25%). First business unit enrolled with push notifications as the default method. Measure registration success, not login success.
- Weeks 5-6: Wave 2 (50%). Add FIDO2 keys for privileged users. Monitor helpdesk queue depth.
- Weeks 7-8: Wave 3 (75%). Remaining knowledge workers. Begin legacy-auth inventory.
- Weeks 9+: Enforcement. Block access for non-enrolled accounts after two-week grace window.
Okta’s deployment data gives the SSO overlay: simple deployments (<100 users) finish in 3-6 weeks, mid-market in 8-12 weeks, complex enterprise in 3-6 months. If a vendor promises “SSO in a weekend” for a 5,000-person org, they’re quoting the pilot, not the rollout.
How Big Is the Legacy Authentication Problem?
Legacy auth, SMTP AUTH, POP, IMAP, ActiveSync Basic, older PowerShell endpoints, is where credential attacks live. Microsoft Learn reports 97% of credential stuffing and 99% of password spray attacks use legacy protocols, and CYE Security found organizations that disable legacy authentication see 67% fewer compromises.
You can’t skip the inventory. Before enforcement, run a legacy-auth discovery report for 30 days. For each discovered client, answer four questions in order: Can it do SAML or OIDC? If not, can it sit behind an authentication proxy? If not, can it be network-isolated? If not, is it end-of-life? That decision tree is the only honest path, anything else is a dated exception waiting to become a breach.
What Happens to Your Helpdesk During Rollout?
Expect a ticket spike. Gartner data reviewed by Cisco Duo attributes up to 50% of helpdesk volume to user lockouts, and F5 Labs cites Forrester’s figure of $87 per password reset. Multiply that by a 5,000-person rollout and the rollout pays for itself in avoided lockouts within a year, if you plan for the spike instead of being surprised by it.
Three mitigations matter more than the rest. Start with low-friction methods like push notifications before requiring hardware keys. Stand up a self-service enrollment portal so users don’t call for routine problems. And staff an MFA war room for the first two weeks of each wave, with direct escalation to identity engineering. Cisco Duo’s guidance is clear: phased rollouts with self-service tooling are the delta between a 3-week spike and a 3-month outage.
Why Does MFA Adoption Lag at Smaller Orgs?
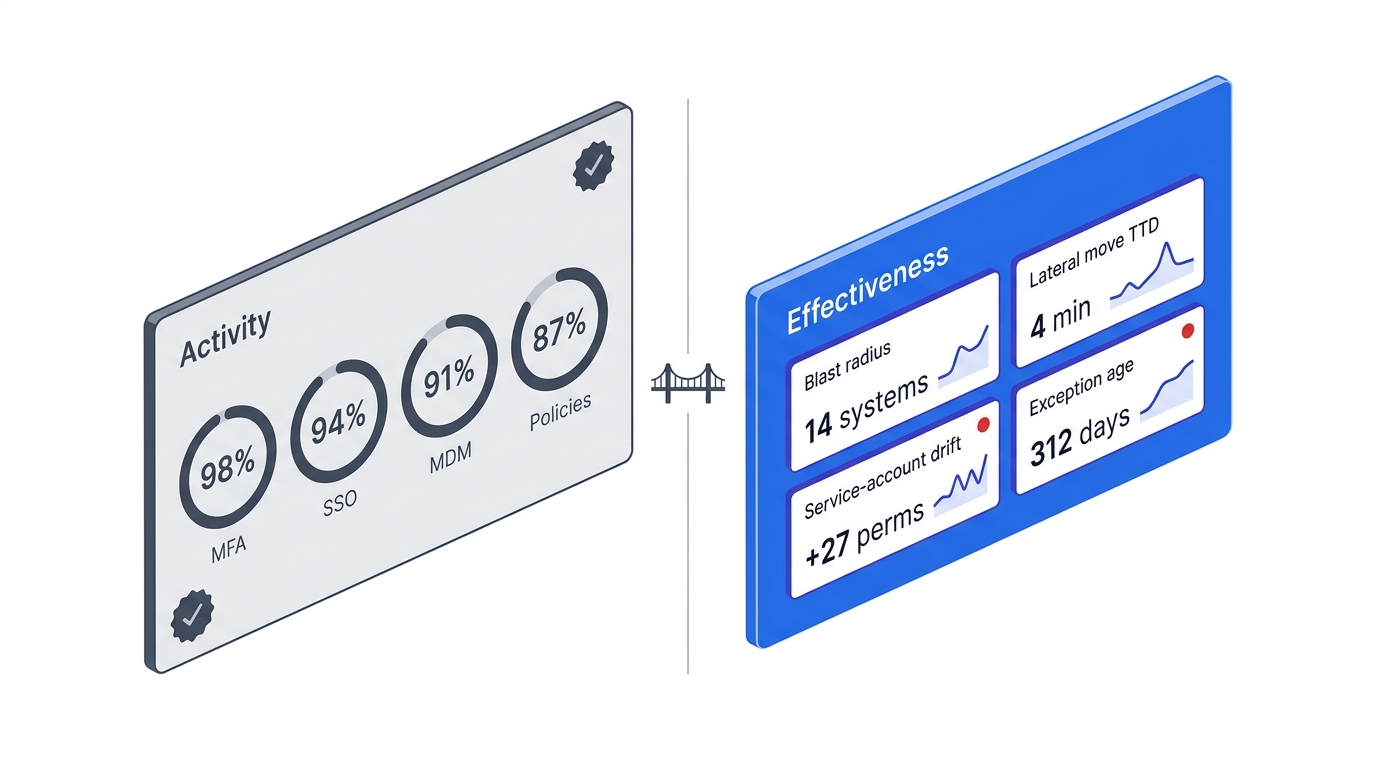
JumpCloud’s 2025 MFA statistics show a predictable gap: 87% adoption at 10,000+ employee orgs, 78% at 1,001-10,000, 34% at 26-100 employees, and 27% at <25. Scoop Market Research corroborates the pattern globally, with 68% of enterprises now implementing MFA versus 54% in 2022.
The gap isn’t about willingness. It’s about identity platform maturity. Large orgs have dedicated IAM teams, small orgs don’t. If you’re scaling between those bands right now, the realistic play is Microsoft Entra ID P1 or Okta Starter Suite, both at roughly $6/user/month, bundled MFA, SSO, and conditional access under one control plane. Buying point MFA and bolting it onto legacy AD is the path most mid-market orgs regret by month 18.
What Does Phase 1 Success Look Like?
By day 30, you should have phishing-resistant MFA enforced for all privileged users, SSO coverage for your top 10 SaaS applications by seat count, and a 30-day legacy-auth discovery report on the steering committee agenda. That’s not the finish line, it’s the baseline. Everything in Phases 2 and 3 assumes these three artifacts exist. Without them, conditional access shadow mode has nothing meaningful to evaluate, and service account triage becomes guesswork.
FAQ
How long does MFA rollout really take for a 5,000-person enterprise?
Plan for 8-12 weeks in 20-25% waves, following the IACIS 2021 case study pattern. Add 3-6 months for full SSO coverage of sanctioned apps per Okta’s methodology. Compressing this timeline almost always costs more in helpdesk overhead than it saves in project duration.
What counts as phishing-resistant MFA in 2026?
CISA designates only two methods as phishing-resistant: FIDO2/WebAuthn (hardware keys, platform authenticators) and PKI-based certificates. SMS, voice, email one-time codes, and push notifications without number matching do not qualify. Microsoft began phasing insecure methods out of its own tenants in September 2025.
Should we deploy SSO or MFA first?
Deploy them together. SSO without MFA centralizes your credentials into a single breach target; MFA without SSO leaves most apps unprotected. Okta’s deployment methodology wraps both into a single identity project, which is the only cost-efficient path for most mid-market and enterprise rollouts.
How do we handle apps that can’t do SAML or OIDC?
Run them through an authentication proxy (Cloudflare Access, Zscaler ZPA, or similar ZTNA product) that fronts the legacy app with modern identity. If the app can’t handle a proxy, isolate it on a dedicated network segment with MFA at the jump host. If neither works, the app belongs on the modernization roadmap covered in our legacy-system strategies.
What MFA adoption rate should we target at 90 days?
For the pilot phase, aim for 90%+ registration among privileged users and 75%+ among general users, with enforcement on privileged accounts and soft-enforcement elsewhere. Microsoft’s own phased rollout safeguards pause enforcement if sign-in success drops below 90%. That’s the threshold to hold yourself to.
How do we stop legacy auth without breaking business workflows?
Run a 30-day discovery report in your identity platform to catalog every legacy-auth client by user, app, and volume. Then work the decision tree: SAML/OIDC upgrade, auth proxy, network isolation, or decommission. Disabling legacy auth reduces compromises by 67%, but only after you’ve inventoried what will actually break.
What does MFA cost per user?
Microsoft Entra ID P1 runs $6/user/month (bundled with many M365 plans), Okta Starter Suite starts at $6/user/month, and FIDO2 hardware keys run $25-50 per device. The helpdesk offset, fewer lockouts at $87 each, typically covers licensing within 12-18 months for most mid-market orgs.
Where This Fits in the 90-Day Playbook
Phase 1 lives or dies on identity. Get MFA, SSO, and legacy-auth discovery into production, then the rest of the playbook has something real to build on. For the full sequence, see the 90-Day Zero Trust Playbook, and for the governance layer that keeps it funded, Building Your Zero Trust Governance Structure. The next Phase 1 chapter, Service Account Triage, addresses the other half of identity: the 82 machine identities per employee that your MFA rollout doesn’t touch.