Building Your Zero Trust Governance Structure
Published
Zero Trust Architecture sounds like a security problem. It’s not. It’s an organizational problem with a security wrapper.
The technical pieces are hard — identity architecture, micro-segmentation, continuous verification — but they’re solvable. What breaks most Zero Trust programs is something much more mundane: unclear ownership, competing priorities across IT and security teams, and governance structures designed for a perimeter security model that no longer exists.
Accenture’s State of Cybersecurity 2025 found that 88% of CISOs report facing significant Zero Trust implementation challenges (CSO Online coverage). Secutor Cybersecurity reports that programs stall most often during periods of organizational change or when governance ownership is ambiguous. Most organizations in this data cite the same root cause: organizational change management and governance, not technical capability.
The structural gap is this: Zero Trust requires decisions across identity, infrastructure, applications, security, and business units. Traditional security governance — where the CISO owns security and IT owns infrastructure — creates a permission matrix with no clear owner when priorities conflict. Programs stall at these boundaries, not at the technical layer.
Key Takeaways
- 88% of CISOs face significant Zero Trust implementation challenges, primarily organizational rather than technical (Accenture State of Cybersecurity 2025)
- Direct executive sponsorship — a committee chair who reports to the CEO or board — is the single strongest predictor of Zero Trust program survival past month six
- RACI clarity for cross-functional decisions (vendor selection, policy exceptions, enforcement go/no-go) eliminates the silent stall points where most programs lose momentum
- The NSA Zero Trust Implementation Guidelines define 91 activities across 5 modular phases; your governance structure must assign ownership to each
- Gartner predicts 75% of US federal agencies will fail to implement Zero Trust through 2026 — enterprise programs built on the same governance assumptions face the same risk (Gartner 2024)
Why Zero Trust Governance Is Non-Standard
Your organization already has governance structures for security, IT operations, and application delivery. Zero Trust sits between all three — and your existing structures probably don’t accommodate that. A CISO who owns security policy, a CIO who owns infrastructure, and business unit leaders who depend on application availability have three different success metrics. Without a governance layer that makes the tradeoffs explicit, the program defaults to the path of least resistance, which is usually doing nothing.
Secutor Cybersecurity found that programs stall most often during organizational change periods or when governance ownership is ambiguous. The data is consistent: governance structure matters more than technology choice.
This means your governance structure needs to be different from your standard IT governance. Standard IT governance optimizes for cost and uptime. Zero Trust governance optimizes for implementing a multi-year architectural shift while maintaining cost and uptime. The tension between those goals requires explicit resolution, which is the job of the steering committee.
The Steering Committee Composition and Roles
The most effective Zero Trust steering committees follow a specific composition:
CTO (Chair). The CTO chairs the committee and owns the Zero Trust program end-to-end. This is not a delegated responsibility. The CTO reports progress directly to the board or CEO, which creates the executive air cover required to settle cross-functional disputes and maintain budget allocation when competing priorities emerge. When a CTO owns Zero Trust, the program’s success becomes directly tied to their performance review.
CISO (Security Architecture Authority). The CISO sets security requirements, defines what “Zero Trust compliance” means for your organization, and owns the policy framework. The CISO does not chair the committee — that role creates bottlenecks when every technical decision requires security sign-off. The CISO’s role is to define the guard rails, not to approve every implementation detail.
Head of Infrastructure (Platform Execution). This person owns the network, identity, and endpoint infrastructure. They’re accountable for actually building the systems that enforce Zero Trust policies. In larger organizations, this might be split between a VP of Network Engineering and a VP of Identity and Access Management, but the principle is the same: whoever owns the infrastructure owns the execution risk.
Head of Applications (App Owner Coordination). Applications are the business value layer, and every Zero Trust decision has application impact. This person ensures that enforcement decisions don’t break business-critical workflows and coordinates with individual app owners on the pilot and rollout schedule.
Business Unit Representative (Business Impact Translation). This person translates business impact back to the steering committee. When infrastructure wants to require hardware-based attestation on all endpoints and applications want to support BYOD, this representative helps the committee understand the business cost of each tradeoff.
Legal/Compliance (Regulatory Alignment). This person ensures that Zero Trust implementation aligns with NIS2, DORA, GDPR, HIPAA, or whatever regulatory framework applies to your organization. They also flag when policy decisions create exposure.
Meeting Cadence and Standing Agenda
Weekly 30-minute meetings during the initial 90-day sprint, structured around a fixed agenda. After the sprint, meetings move to bi-weekly. Discipline on agenda and time is non-negotiable — long, open-ended meetings are where steering committees die.
Standing Agenda (30 minutes total):
-
Progress by Phase (8 minutes). One-line update on each active workstream (e.g., “Identity platform selected, procurement in progress”). Red/yellow/green status only. No deep dives — exceptions go to exception review.
-
Exception Review (12 minutes). Escalated blockers that need steering committee decision. One decision per meeting. If a decision can’t be made in 12 minutes with the people in the room, it’s not escalated here — it goes to a working group and comes back when ready.
-
Blocker Escalation (5 minutes). Dependencies on external teams or other initiatives. Raise them, assign owner, move forward.
-
Budget Tracking (5 minutes). Actual spend versus forecast. Are we on track? Do we need to reforecast?
This structure is boring, which is exactly right. Boring steering committees that make decisions and move forward are far more effective than exciting ones that discuss strategy at length without resolving anything.
RACI Matrix for Zero Trust Decisions
A RACI matrix for common Zero Trust decisions removes ambiguity about who decides what. This is the governance tool that actually accelerates implementation.
| Decision | Responsible | Accountable | Consulted | Informed |
|---|---|---|---|---|
| Identity Platform Selection | Security Architect | CISO | Platform Team | CTO, Business Unit Rep |
| Policy Exception Approvals | Application Owner | CISO | Legal | CTO |
| Enforcement Go/No-Go Decision | Platform Team Lead | CTO | CISO, App Owners | Business Unit Rep |
| Vendor/Product Selection | Security Architect | CTO | CISO, Procurement | Legal |
| Budget Reallocation Mid-Year | Program Lead | CTO | Finance | Steering Committee |
| Incident Response Policy Changes | CISO | CTO | Platform Team | Legal |
| Micro-segmentation Scoping | Platform Team | Head of Infrastructure | CISO | App Owners |
| Logging and Audit Requirements | CISO | Head of Infrastructure | Compliance | Finance |
| Pilot Workload Selection | App Owners | CTO | Platform Team | CISO |
| Rollout Timeline Decisions | Program Lead | CTO | App Owners, Infrastructure | Finance |
Each cell specifies:
- R (Responsible): Who does the work.
- A (Accountable): Who owns the decision and its outcome. Only one person per decision.
- C (Consulted): Who gives input before the decision is made.
- I (Informed): Who needs to know the decision, but doesn’t need to be involved.
This matrix is not theory. It’s the practical tool that stops meetings from being 90 minutes of debate with no decision. You consult the people in the C column, the A person decides, and the R person executes. The I people get a status update. Done.
NSA ZIGs: 91 Activities, 5 Modular Phases
The NSA’s Zero Trust Implementation Guidelines (published 2024) define 91 specific activities organized across 5 modular phases: Zero Trust Identification and Assessment, Zero Trust Architecture Design, Zero Trust Security Capability Implementation, Zero Trust Operational Validation, and Zero Trust Continuous Monitoring.
Your governance structure needs to map execution ownership to each phase and assign someone accountable for progress. You don’t need to do all 91 activities — organizations vary in maturity, industry, and regulatory obligations. But you do need someone who is responsible for each activity you’ve committed to. That accountability rolls up through the steering committee to the CTO.
This is where governance meets rigor. The steering committee’s job isn’t to know the details of all 91 activities. It’s to ensure that ownership is assigned, progress is tracked, and decisions are made when activities hit blockers.
Why Programs Stall: The Data
The failure data is specific. Gartner reports that 63% of organizations have implemented a Zero Trust strategy, but only a fraction reach full maturity. Gartner also predicts that 75% of US federal agencies will fail to implement Zero Trust policies through 2026 — a cohort with more budget, more mandates, and more oversight than most enterprises, yet still failing. Accenture’s 2025 research finds 88% of CISOs struggling with execution. The data isn’t about technology — it’s about governance.
When you dig into the failure narratives, the pattern is always the same:
-
Undefined ownership. The program sat between IT and security with no clear owner. Decisions took 60+ days. Budget got reallocated to emergencies.
-
No success metrics. After 18 months, the organization couldn’t articulate what they’d accomplished. The board cut funding.
-
Scope creep. The program tried to implement ZTA across all 91 NSA activities simultaneously. It ran out of budget and talent before meaningful progress was visible.
-
Vendor lock-in paralysis. The organization spent 12 months evaluating identity platforms and never made a decision.
-
Application impact underestimated. Zero Trust enforcement broke business-critical workflows, and there was no app owner in the room to catch it before it went to production.
Every one of these failure modes is governance-related, not technology-related. And every one is preventable with the right steering committee structure and RACI clarity.
From Theory to Practice: 90-Day Sprint Governance
Your first 90 days should establish governance, lock in quick wins on identity (MFA, privileged access management), and create the foundation for 18-month program phases. The steering committee’s job during these 90 days is to make weekly decisions and clear obstacles in real-time.
For a detailed 90-day implementation roadmap, see 90-Day Zero Trust Playbook. For app-level prioritization, see Application Criticality Scorecard.
Exception Management: Policy vs. Implementation
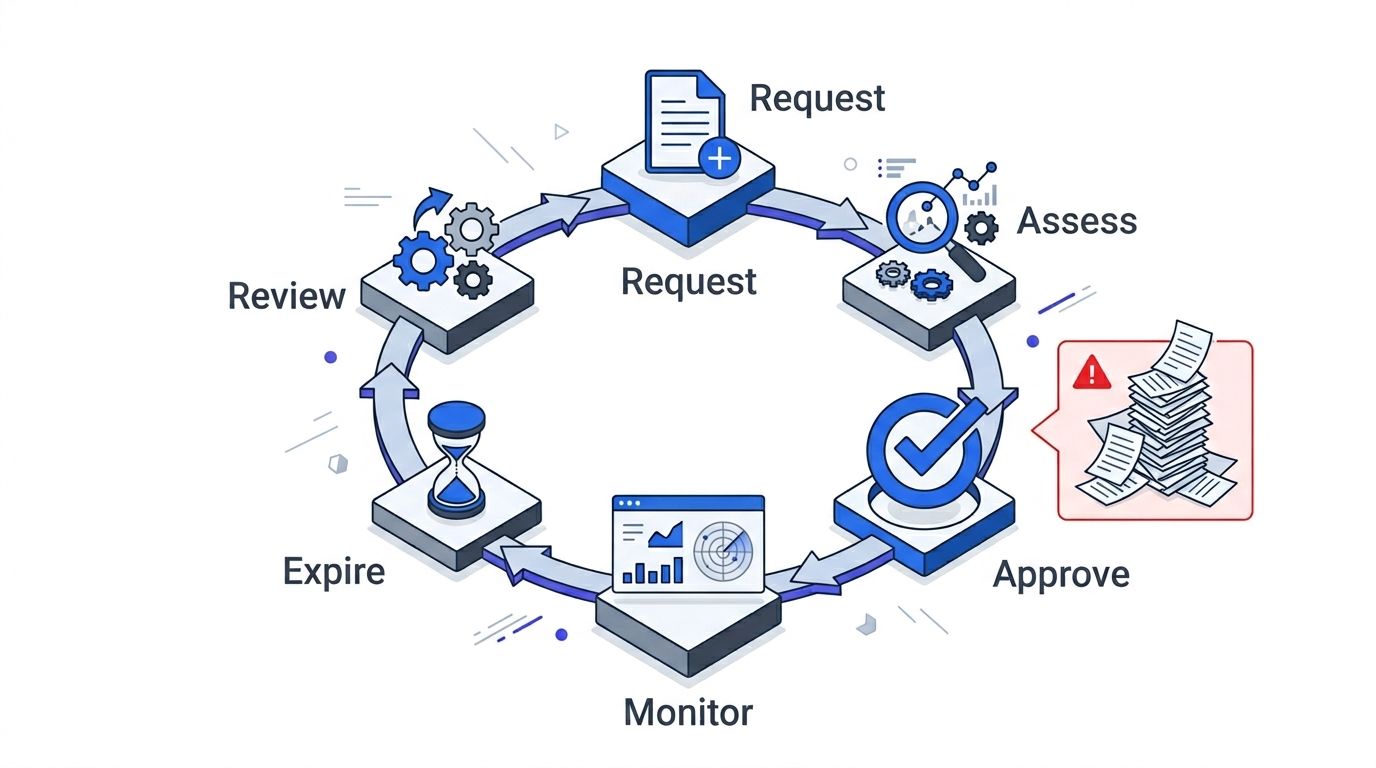
One governance decision will dominate your first year: policy exceptions. Zero Trust is built on the principle of least privilege — users and systems get only the access they need. But “need” is a business decision, not a security decision. When a legacy application can’t be updated and requires overly broad network access, that’s an exception.
Your governance structure must have a clear path for exception approval that doesn’t require the CTO’s personal sign-off every time. The RACI matrix above specifies that app owners submit exceptions, the CISO approves, and legal is consulted. That process should take one week, not eight.
For exception management framework and templates, see Zero Trust Exception Management.
Connecting to Baseline Metrics
Your steering committee also owns success metrics. By the end of the 90-day sprint, you should have:
- Identity coverage: Percentage of user sessions secured by MFA + risk-based conditional access.
- Network segmentation: Percentage of critical systems behind micro-segmentation policies.
- Incident response time: Hours to detect and respond, with a target for 20% improvement.
- Policy exception rate: Number of exceptions per 1,000 users as a leading indicator of workflow impact.
These metrics aren’t nice to have. They’re the proof points you take to the board when budget cycles renew. For detailed metrics guidance, see Baseline Metrics Framework.
Governance Prevents Execution Failure
The pattern across successful Zero Trust programs is not more sophisticated technology or more vendor innovation. It’s governance clarity: one person owns the program, the steering committee makes weekly decisions, RACI matrices eliminate ambiguity, and metrics track progress.
Most organizations are struggling because they have a security strategy but no governance structure to execute it. The 10% that are reaching full Zero Trust maturity have solved the governance problem first — executive ownership, weekly cadence, and explicit RACI. The other 90% are still negotiating who decides.
Start with governance. The technology will follow.
Continue with:
- 90-Day Zero Trust Playbook — detailed sprint roadmap and execution patterns
- Application Criticality Scorecard — prioritization framework for pilot workload selection
- Baseline Metrics Framework — measurement framework for tracking progress and proving ROI
- Executive Guide — the business and regulatory context
- Technology Deep Dive — implementation patterns for each Zero Trust pillar