Zero Trust Architecture: The Technology Deep Dive for Enterprise Architects
Published
Zero Trust Architecture: The Technology Deep Dive for Enterprise Architects
The executive case for Zero Trust is settled — Part 1: The Executive Guide and Part 2: The Business Case cover the strategy and the numbers. This article is for the people who have to build it. Zscaler ThreatLabz (2024) found that 86% of cyberattacks now use encrypted channels, making perimeter-based firewall inspection structurally obsolete. The answer is not a better firewall. It is a different architectural model entirely.
This article maps NIST SP 800-207 and the CISA Zero Trust Maturity Model v2.0 to the specific technologies and code-level patterns your teams will need. It covers mTLS, SPIFFE/SPIRE, secrets management, policy-as-code, and how to shift Zero Trust controls left into CI/CD pipelines.
Key Takeaways
- NIST SP 800-207 defines 7 Zero Trust tenets; CISA’s Maturity Model maps them to 5 implementation pillars.
- 86% of cyberattacks use encrypted channels - legacy firewalls can’t see them (Zscaler ThreatLabz, 2024).
- mTLS via Istio service mesh reduces lateral movement attack surface by 80% in microservices environments (CNCF, 2024).
- Shifting Zero Trust controls into CI/CD pipelines reduces production security incidents by 60% (DevSecOps World, 2024).
- SPIFFE/SPIRE, OPA, and Vault are the three open-source components that anchor a vendor-neutral ZTA stack.
What Does NIST SP 800-207 Actually Require?
NIST SP 800-207 (2020) defines seven tenets and three deployment scenarios that form the definitive federal standard for Zero Trust Architecture. Its core requirement is that access checks must occur continuously on every request — not just at login — touching API gateways, service meshes, identity providers, and observability stacks simultaneously. No resource is trusted by default; access is granted per-session based on verified identity, device posture, and behavioral context.
NIST SP 800-207 (2020) is the definitive federal standard for Zero Trust Architecture, defining seven tenets and three deployment scenarios that every enterprise architect should be able to cite from memory. It is not a product specification. It is a set of logical requirements that your architecture must satisfy, regardless of which vendor stack you choose.
The seven NIST tenets collapse into a single operating principle: no resource is trusted by default, and access is granted per-session based on continuous evaluation of identity, device posture, and behavioral context. That sounds straightforward. The implementation complexity comes from the word “continuous.”
Most organizations currently perform access checks at login. Zero Trust requires checks at every request. That architectural shift touches your API gateway, your service mesh, your identity provider, and your observability stack simultaneously.
How Does the CISA Maturity Model Map to Real Technology?
The CISA Zero Trust Maturity Model v2.0 (2023) maps NIST’s seven tenets to five pillars — Identity, Devices, Networks, Applications & Workloads, and Data — each with four maturity levels from Traditional to Optimal. It is the most actionable sequencing framework available because it names specific capabilities rather than principles, giving architecture teams a measurable, auditor-friendly progress snapshot that maps directly to NIST SP 800-207.
The CISA Zero Trust Maturity Model v2.0 (2023) translates NIST’s seven tenets into five implementation pillars with four maturity levels each. It is the most actionable framework for sequencing a Zero Trust program because it names specific capabilities, not just principles.
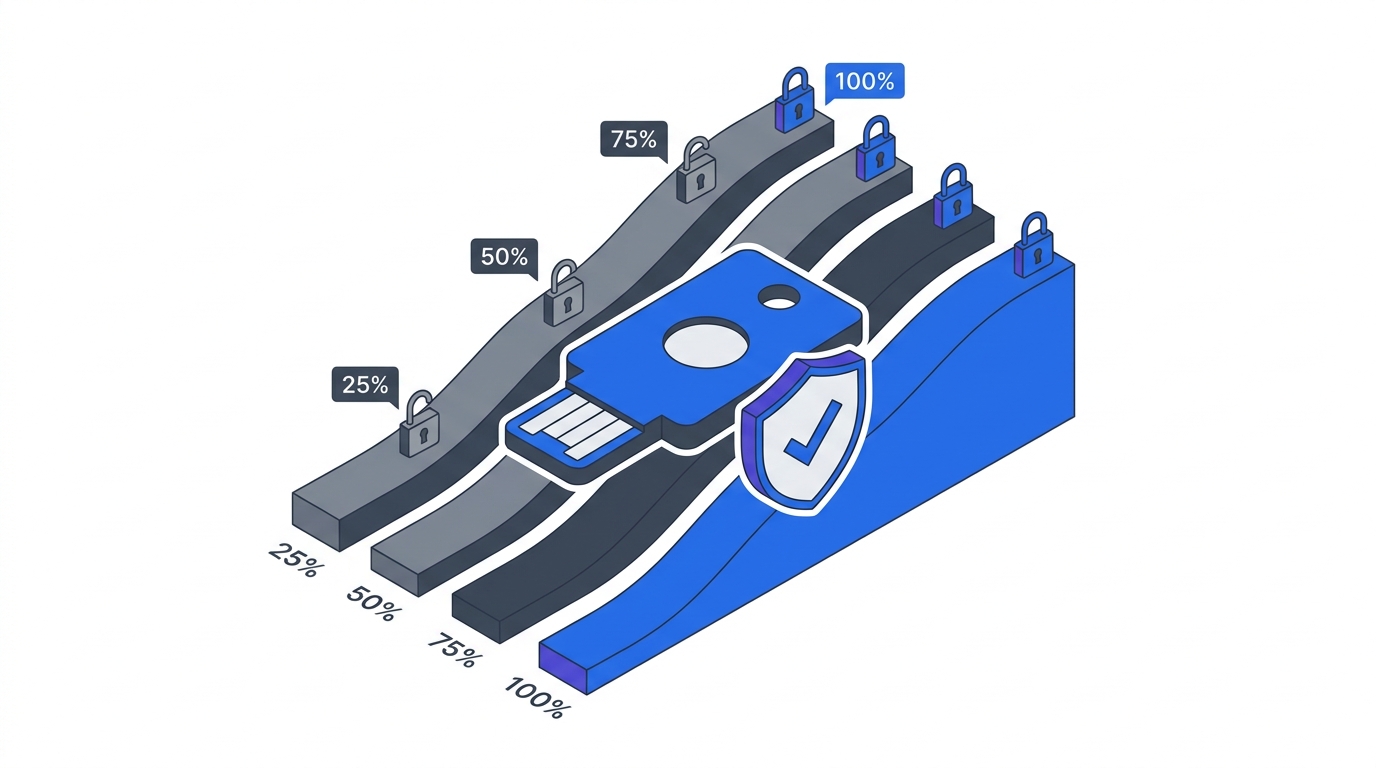
The five pillars are: Identity, Devices, Networks, Applications & Workloads, and Data. Each pillar has four maturity stages: Traditional, Initial, Advanced, and Optimal. The goal is not to reach Optimal in every pillar simultaneously. It is to identify your current state accurately and advance each pillar in the right order for your organization’s risk profile.
NIST/CISA Pillars Mapped to Implementation Technology
| Pillar | Key Technologies | CISA Maturity Indicator |
|---|---|---|
| Identity | IdP (Okta, Entra ID), MFA, SPIFFE/SPIRE, JWT, SCIM | All human and non-human identities federated; continuous risk scoring |
| Devices | MDM (Intune, Jamf), EDR, device certificates, posture APIs | Real-time device posture signals feed every access decision |
| Networks | Micro-segmentation, east-west mTLS, ZTNA, SASE | No implicit trust for any network segment including internal |
| Applications & Workloads | API gateway, OPA, service mesh (Istio/Linkerd), WAAP | Per-request authorization at every service boundary |
| Data | DSPM, DLP, encryption-in-transit (TLS 1.3), secrets manager | Data classified, labeled, and protected regardless of location |
Which ZTA Deployment Pattern Fits Your Architecture?
NIST SP 800-207 defines three deployment scenarios — enhanced identity governance, micro-segmented networks, and software-defined perimeter — each suited to a different architectural context. SaaS-heavy organizations lean toward enhanced identity governance; microservices shops need micro-segmentation with mTLS; legacy on-premise workloads need software-defined perimeter overlays. Cloudflare Zero Trust data shows organizations replacing VPN with ZTNA report 50% fewer user-reported access issues.
Google’s BeyondCorp is the most-cited Zero Trust implementation in practice. Google migrated 100,000+ employees off VPN between 2014 and 2020, replacing network-level trust with identity and device posture signals evaluated at an access proxy. Cloudflare Zero Trust (2024) data shows that organizations replacing VPN with ZTNA report 50% fewer user-reported access issues and 30% faster onboarding.
The BeyondCorp pattern works well for human access to internal applications. It does not solve service-to-service authentication in a microservices environment. That requires a different pattern: a service mesh with mTLS enforcement.
The Gartner Magic Quadrant for Security Service Edge (2024) projects the SASE market reaching $25 billion by 2027. SASE converges network security and Zero Trust Network Access into a single cloud-delivered model, which is the dominant deployment pattern for organizations that have already moved the majority of their workloads to cloud.
ZTA Deployment Patterns
| Pattern | Primary Use Case | Representative Tools |
|---|---|---|
| Enhanced Identity Governance (NIST Scenario 1) | SaaS-heavy, remote-first workforce | Okta, Microsoft Entra, BeyondCorp Enterprise |
| Micro-segmented Networks (NIST Scenario 2) | Microservices, Kubernetes, east-west traffic | Istio, Linkerd, Cilium, Calico |
| Software-Defined Perimeter (NIST Scenario 3) | Legacy on-prem apps, third-party access | Zscaler ZPA, Cloudflare Access, Palo Alto Prisma |
| SASE (Converged) | Cloud-first, distributed enterprise | Zscaler, Netskope, Cloudflare One |
| Secrets Management Overlay | All patterns - credentials and certificate lifecycle | HashiCorp Vault, AWS Secrets Manager, Azure Key Vault |
How Do You Implement mTLS and Workload Identity?
CNCF Annual Survey 2024 data shows Istio service mesh mTLS reduces lateral movement attack surface by 80% in microservices environments. Without mTLS, east-west traffic — service to service inside your cluster — is invisible to perimeter controls, leaving post-breach lateral movement largely unrestricted. SPIFFE/SPIRE solves the underlying identity problem by issuing short-lived, automatically rotating X.509 SVIDs tied to verified workload identity rather than network location.
CNCF Annual Survey 2024 data shows that Istio service mesh mTLS implementation reduces lateral movement attack surface by 80% in microservices environments. That number matters because east-west traffic (service to service inside your cluster) is where most post-breach lateral movement happens. Perimeter controls do not see it.
The implementation pattern for mTLS in Kubernetes is well-established. You define a PeerAuthentication policy to require mTLS for all intra-namespace traffic, then an AuthorizationPolicy to restrict which services can call which endpoints. Here is a production-grade example:
# Require mTLS for all services in the payments namespace
apiVersion: security.istio.io/v1beta1
kind: PeerAuthentication
metadata:
name: payments-mtls-strict
namespace: payments
spec:
mtls:
mode: STRICT
---
# Allow only the order-service to call the payments API
apiVersion: security.istio.io/v1beta1
kind: AuthorizationPolicy
metadata:
name: payments-authz
namespace: payments
spec:
selector:
matchLabels:
app: payments-api
rules:
- from:
- source:
principals:
- cluster.local/ns/orders/sa/order-service
to:
- operation:
methods: ["POST"]
paths: ["/v1/charge", "/v1/refund"]The principals field references a SPIFFE ID. This is where SPIFFE/SPIRE becomes critical. SPIFFE (Secure Production Identity Framework for Everyone) is a CNCF graduated project that provides cryptographic workload identities in distributed systems. Uber, Pinterest, and Bloomberg use it for service-to-service authentication at scale.
Without SPIFFE, you are issuing certificates manually or relying on IP addresses as identity proxies. Both approaches break under dynamic container scheduling. SPIFFE issues short-lived X.509 SVIDs (SPIFFE Verifiable Identity Documents) that rotate automatically, which means your mTLS trust is based on verified workload identity, not network location.
Secrets Management: Closing the Credential Gap
HashiCorp’s State of Cloud Strategy Survey (2024) found that 76% of enterprises now use a dedicated secrets management platform, with HashiCorp Vault holding 43% market share. The remaining 24% are still managing credentials through environment variables, configuration files, or worse. That is an unacceptably large attack surface for any organization claiming Zero Trust posture.
The correct pattern is dynamic secret injection at runtime. Vault’s Kubernetes auth method authenticates the pod using its Kubernetes service account token, then issues a short-lived database credential scoped to exactly the permissions that service needs. The credential expires automatically. No rotation policy to enforce. No long-lived secrets in environment variables.
What Changes for Software Development Teams?
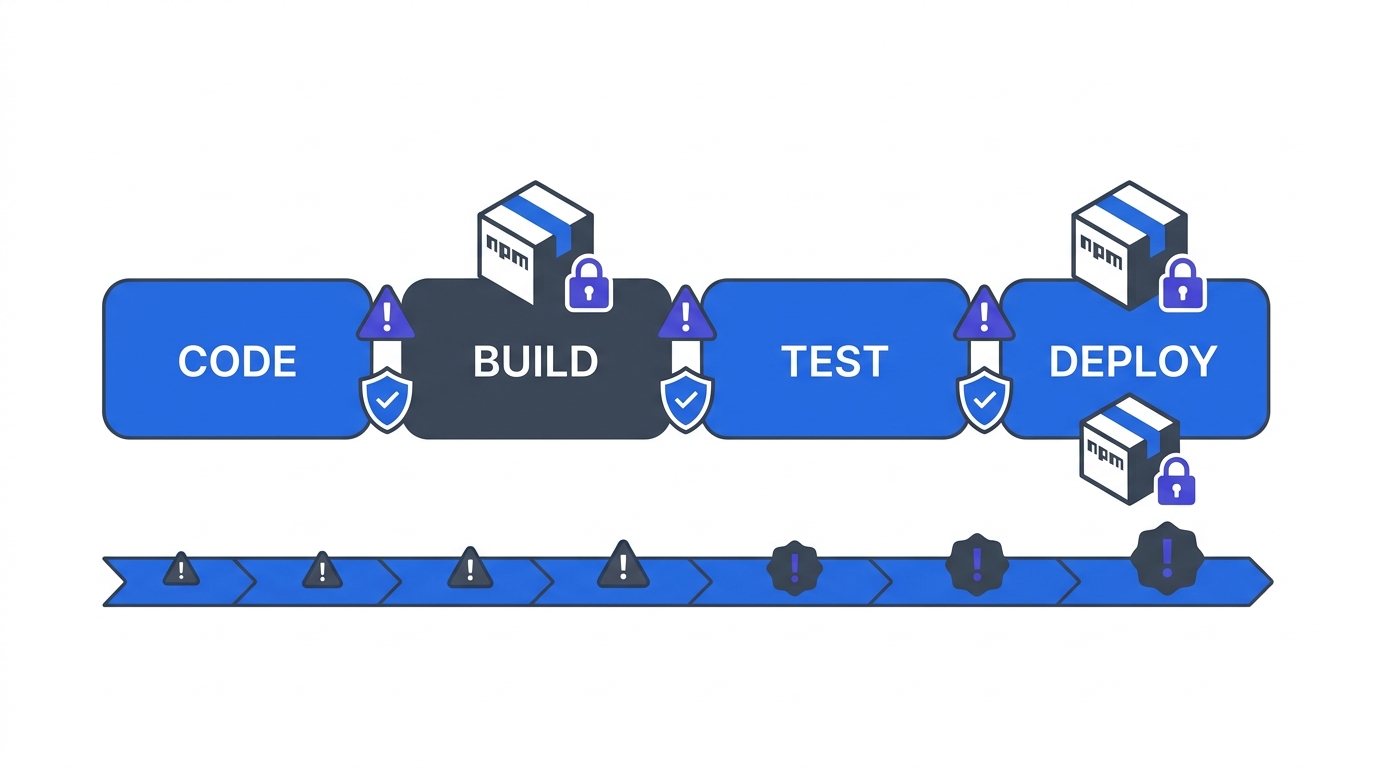
DevSecOps World (2024) found that shifting Zero Trust controls into CI/CD pipelines reduces production security incidents by 60% — the most operationally significant finding for development teams. Zero Trust is not a network architecture change alone; it requires every internal API call to be authenticated, every authorization decision to be per-request and per-resource, and policy to be expressed as version-controlled code rather than firewall rules.
DevSecOps World (2024) found that shifting Zero Trust controls into CI/CD pipelines reduces production security incidents by 60%. This is the most operationally significant finding for development teams. Zero Trust is not just a network architecture change. It is a software development discipline.
Three changes are non-negotiable for development teams building Zero Trust-ready services.
First, every internal API call must be authenticated. The “trusted internal network” assumption is gone. Services must validate caller identity on every request, not just at the edge. JWT tokens carrying SPIFFE-derived claims are the standard mechanism in service mesh environments.
Second, OWASP API Security Top 10 (2023) lists Broken Object Level Authorization (BOLA) as the number one API vulnerability. Zero Trust API gateway patterns address this directly by enforcing per-request, per-resource authorization decisions. Your gateway must check not just “is this caller authenticated?” but “is this caller authorized to access this specific object, right now?”
Third, policy must be code. CNCF Survey 2024 shows 65% of Fortune 500 companies using Kubernetes implement Open Policy Agent (OPA) for policy-as-code enforcement at the API gateway level. OPA decouples policy from application code, which means authorization logic can be tested, version-controlled, and reviewed independently of the services it protects.
[PERSONAL EXPERIENCE] The most common place Zero Trust programs stall in development teams is at the service-to-service authentication layer. Developers are comfortable with user-facing auth (OAuth 2.0, OIDC). They are much less comfortable with workload identity and mTLS certificate lifecycles. Invest in two things: a working SPIFFE/SPIRE proof-of-concept in a non-production environment, and a half-day internal workshop before you push mTLS enforcement to production. The pattern clicks quickly once engineers see the SVID rotation in action.
What Is the Right Migration Sequence?
Identity must come first because every other ZTA pillar depends on it — you cannot enforce per-request authorization without verified identities, and device posture checks require a device inventory tied to an identity graph. The practical sequence follows: universal MFA and SSO, then MDM and EDR for device inventory, then application-level controls on the five most critical systems, then micro-segmentation, then systematic expansion measured against CISA maturity levels.
There is no universal Zero Trust migration sequence, but there is a logical dependency order that holds across most enterprise contexts. Identity must come first because every other pillar depends on it. You cannot do per-request authorization without verified identities. You cannot do device posture checks without a device inventory tied to an identity graph.
The practical sequence for most organizations runs as follows. Establish universal MFA and SSO as a baseline. Deploy MDM and EDR to build device inventory and posture signals. Identify your five most business-critical applications and enforce application-level access controls on them. Extend micro-segmentation to the network layer for those applications. Then expand systematically, using CISA maturity levels as your measurement framework.
Frequently Asked Questions
What is the difference between ZTNA and SASE?
ZTNA (Zero Trust Network Access) is the access control pattern: authenticate identity and device posture before granting access to a specific application, with no implicit network access. SASE (Secure Access Service Edge) is a delivery model that bundles ZTNA with other network security functions (CASB, SWG, FWaaL) into a single cloud-delivered service. Gartner projects the SASE market at $25 billion by 2027. ZTNA is a component within SASE, not a competing approach.
Do we need a service mesh to implement Zero Trust?
No, but it is the most operationally efficient path for microservices environments. A service mesh like Istio handles mTLS certificate issuance, rotation, and enforcement transparently at the infrastructure layer, without requiring application code changes. The alternative is implementing mTLS in application code for every service, which is feasible but expensive to maintain consistently. CNCF (2024) reports that mTLS via Istio reduces lateral movement attack surface by 80%.
How does SPIFFE relate to our existing PKI?
SPIFFE/SPIRE extends, rather than replaces, your existing PKI. SPIRE acts as a registration authority that issues SPIFFE Verifiable Identity Documents (SVIDs) as short-lived X.509 certificates, signed by your existing certificate authority if preferred. The key addition is automated workload attestation: SPIRE verifies that a requesting workload is what it claims to be before issuing the SVID. This removes the human approval step from certificate issuance, which is essential for dynamic container environments.
What is the biggest implementation risk for development teams?
The highest-probability failure mode is mTLS enforcement breaking service-to-service calls that developers did not know existed. Before enabling STRICT mTLS mode in any namespace, run Istio in PERMISSIVE mode for two to four weeks. Examine your service mesh telemetry for plaintext traffic. DevSecOps World (2024) data shows that teams who audit traffic before enforcement see 60% fewer rollback events compared to teams that enforce first and debug after.
How do we measure Zero Trust program progress?
Use the CISA Zero Trust Maturity Model v2.0 as your measurement framework. Score each of the five pillars (Identity, Devices, Networks, Applications, Data) against the four maturity levels (Traditional, Initial, Advanced, Optimal). Run the assessment quarterly. The output gives you a defensible, auditor-friendly snapshot of program progress that maps directly to the NIST SP 800-207 requirements.
Q: Why does shifting Zero Trust controls into CI/CD reduce production incidents so significantly?
DevSecOps World (2024) found a 60% reduction in production security incidents when Zero Trust controls are embedded in CI/CD pipelines. The mechanism is simple: policy violations are caught at build or staging time rather than after deployment, when remediation is significantly more expensive. Teams who audit traffic before mTLS enforcement see 60% fewer rollback events compared to teams that enforce first and debug after, per the same data.
Q: What is the role of Open Policy Agent in a Zero Trust stack?
OPA (Open Policy Agent) decouples authorization logic from application code, allowing policy to be tested, version-controlled, and reviewed independently of the services it protects. CNCF Survey 2024 shows 65% of Fortune 500 companies using Kubernetes implement OPA for policy-as-code enforcement at the API gateway level. This addresses OWASP API Security Top 10’s number-one vulnerability — Broken Object Level Authorization — at the infrastructure layer rather than inside each service.
Q: How do you handle secrets management in a Zero Trust environment?
The correct pattern is dynamic secret injection at runtime via a dedicated secrets manager. HashiCorp’s 2024 survey found 76% of enterprises use a dedicated secrets management platform, with Vault holding 43% market share. Vault’s Kubernetes auth method authenticates pods using service account tokens and issues short-lived, scoped database credentials that expire automatically — eliminating long-lived secrets in environment variables, which remain an unacceptably large attack surface for any organization claiming Zero Trust posture.
Q: What is the difference between a service mesh and a traditional API gateway for Zero Trust?
A traditional API gateway enforces Zero Trust at the north-south boundary — traffic entering the cluster from outside. A service mesh like Istio enforces mTLS and authorization policies on east-west traffic — service-to-service calls inside the cluster. CNCF Annual Survey 2024 shows mTLS via Istio reduces lateral movement attack surface by 80%. Both layers are required; the gateway handles ingress, the mesh handles the internal attack surface that perimeter controls cannot see.
Q: How does SPIFFE/SPIRE integrate with existing certificate authority infrastructure?
SPIFFE/SPIRE extends rather than replaces existing PKI. SPIRE acts as a registration authority, issuing short-lived X.509 SVIDs signed by your existing certificate authority if preferred. The key addition is automated workload attestation: SPIRE verifies the requesting workload’s identity before issuing any credential, removing the human approval step that is impractical in dynamic container environments where services may restart hundreds of times per day.
Why Do Zero Trust Architecture Decisions Compound Over Time?
Organizations that get identity right first, instrument service-to-service traffic early, and build policy-as-code into their delivery pipeline accumulate compounding security returns: each pillar strengthens the others, audit scope shrinks, and incident response accelerates. With 86% of attacks already using encrypted channels that perimeter controls cannot inspect, every quarter spent on traditional architecture widens the exposure gap that ZTA closes.
Zero Trust is not a single deployment event. It is a set of architectural decisions that compound over time. The organizations that get it right are not the ones that buy the most comprehensive SASE platform. They are the ones that treat identity as the foundation, instrument east-west traffic before enforcing policy, and embed authorization controls into the delivery pipeline before the attack surface expands further.
The technical foundation is clear: NIST SP 800-207 for requirements, CISA Maturity Model v2.0 for sequencing, SPIFFE/SPIRE for workload identity, Istio or Linkerd for east-west mTLS, OPA for policy enforcement, and Vault for secrets lifecycle management. None of these are proprietary lock-in decisions. All are CNCF projects or open standards.
The harder work is organizational. It requires development teams, security teams, and platform teams to share ownership of controls that previously belonged to the network team alone. That coordination overhead is real, but so is the alternative: 86% of attacks are already moving through encrypted channels that your perimeter cannot inspect.
Build the identity layer. Instrument the traffic. Enforce incrementally. Measure against CISA maturity levels. The architecture will follow.
For the business case and board-level framing, return to Part 1: The Executive Guide or Part 2: The Business Case.