Zero Trust Architecture: The Executive Guide for 2026
Published
Most organizations have heard of Zero Trust Architecture. A striking number have even started implementing it. But there’s a gap between “started” and “finished” that should concern every executive with a seat at the table when security budgets come up for review.
According to Gartner (April 2024), 63% of organizations worldwide have implemented some form of Zero Trust strategy. Yet a separate Gartner forecast predicts only 10% of large enterprises will have a mature, measurable program in place by 2026. That’s the adoption gap, and it costs real money.
This guide explains what Zero Trust Architecture actually means, why the maturity gap exists, how government mandates are raising the stakes, and what a board-level conversation about ZTA should look like in 2026. For the financial case and regulatory exposure, Part 2: The Business Case covers the board-level numbers. Part 3: Technology Deep Dive maps the implementation path for enterprise architects.
Key Takeaways
- The average data breach cost $4.88M in 2024, a 10% year-on-year increase (IBM, 2024)
- Organizations with mature Zero Trust programs averaged $1.76M less per breach than those without
- 63% of organizations have started a Zero Trust strategy, but only 10% will have a mature program by 2026
- US federal agencies were required to meet Zero Trust goals by end of FY2024 — private sector ripple effects are already visible
- By 2028, 50% of organizations will adopt Zero Trust data governance as AI-generated data grows
Why “Never Trust, Always Verify” Has Become Non-Negotiable
Data breaches now cost an average of $4.88M per incident — a 10% year-on-year rise — and 70% of breached organizations report significant operational disruption, according to IBM’s 2024 report. With compromised credentials going undetected for an average of 292 days inside trusted networks, the implicit-trust perimeter model has demonstrably failed.
The traditional security perimeter is gone. Data breaches now cost an average of $4.88M per incident in 2024, a 10% increase over the prior year, according to IBM. That figure climbs further when you factor in business disruption: 70% of breached organizations experienced significant or very significant operational impact.
The perimeter model assumed that threats came from outside. Put a firewall around the castle, and everyone inside is trusted. That assumption broke down over the past decade for three reasons.
First, the perimeter dissolved. Remote work, cloud infrastructure, SaaS applications, and BYOD policies mean there’s no longer a clear boundary to defend. An employee working from a coffee shop in Warsaw connects to the same systems as one sitting in headquarters.
Second, threats are now internal as often as external. Compromised credentials account for 16% of all breaches, and when credentials are stolen, attackers go undetected for an average of 292 days, according to IBM’s Cost of a Data Breach Report 2024. Nearly ten months of undetected access, inside your trusted network.
Third, the regulatory environment shifted. Beginning with the US Executive Order 14028 in 2021 and accelerating through OMB M-22-09 in 2022, governments started treating Zero Trust not as a best practice but as a requirement.
A Brief History: From Kindervag to NIST
The term “Zero Trust” was coined by Forrester Research analyst John Kindervag in 2010. His core insight was simple: implicit trust is a vulnerability. Every user, device, and network connection should be treated as potentially hostile until verified otherwise.
The concept gained formal codification in NIST Special Publication 800-207, published in 2020. That document gave enterprises and regulators a shared vocabulary and a framework for implementation. It remains the canonical definition today.
In January 2026, the NSA published the Zero Trust Implementation Guideline Primer — a companion to a phased set of Implementation Guides (ZIGs) covering 152 activities across 42 capabilities organised into Discovery, Phase One, Phase Two (Target-level), and Phase Three / Four (Advanced-level). It is the most concrete public-sector evidence to date that Zero Trust is treated as a structured, multi-year programme rather than a product procurement — and the activity counts are a useful realism check on any “we’ll have ZT done by Q3” plan.
What Zero Trust Architecture Actually Means (Beyond the Buzzword)
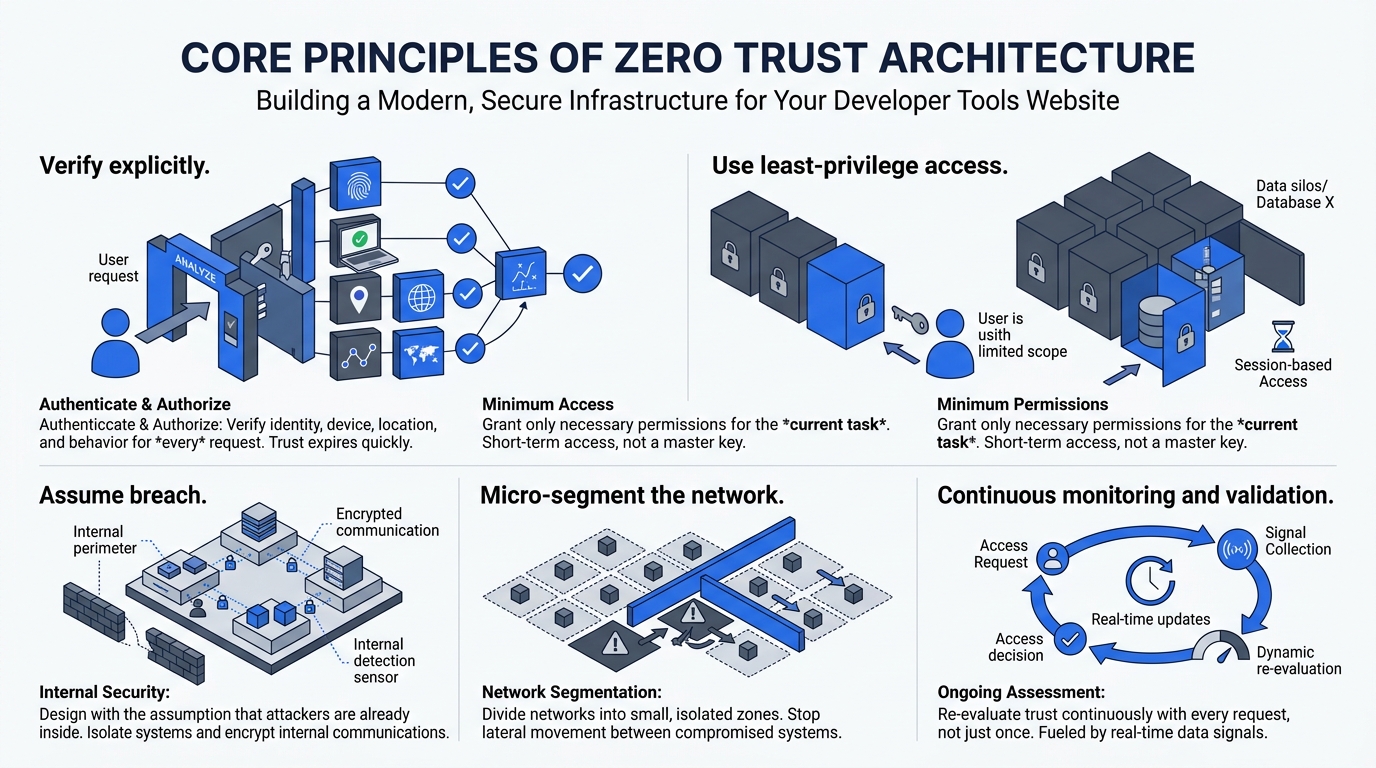
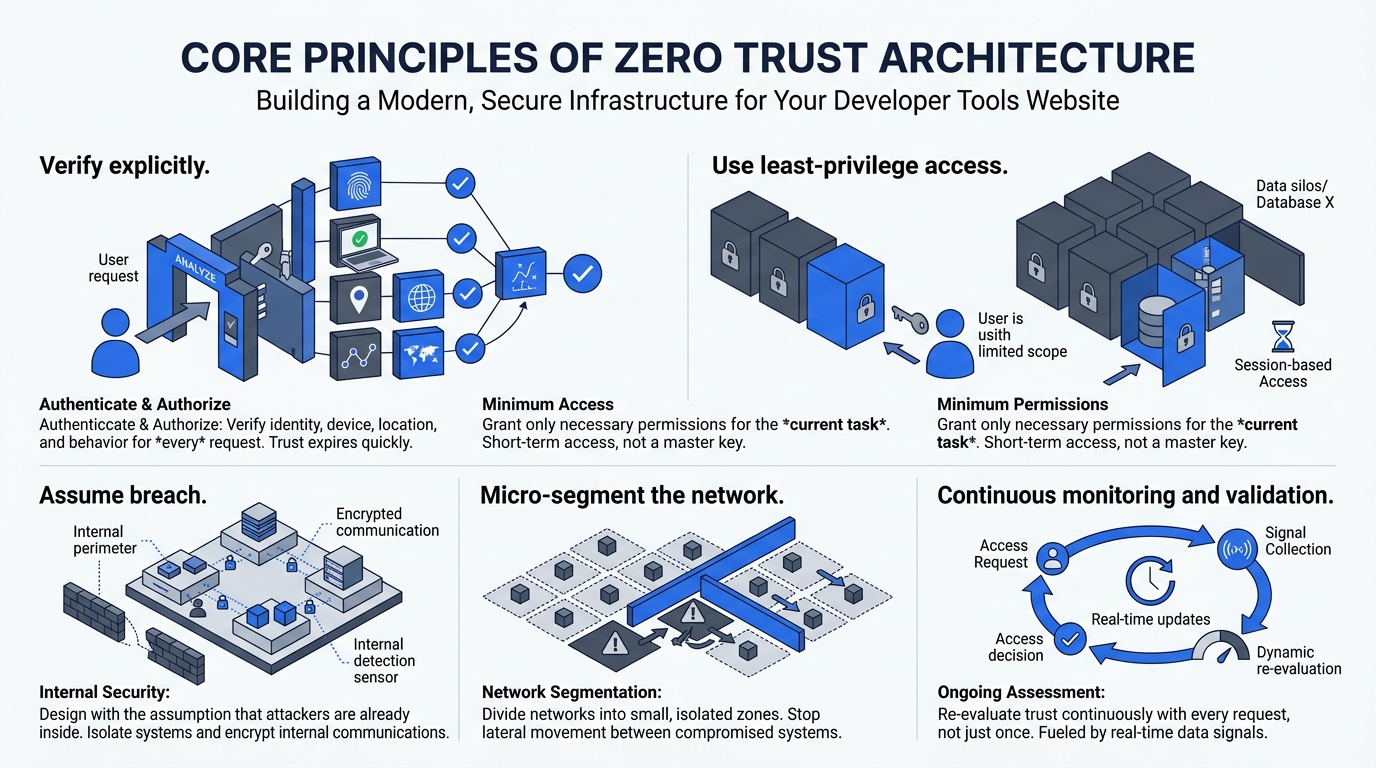
Zero Trust Architecture is defined by NIST SP 800-207 as a continuous-verification model built on five operational principles: verify explicitly, use least-privilege access, assume breach, micro-segment the network, and monitor continuously. Credentials stolen in a traditional perimeter environment grant attackers an average of 292 undetected days; Zero Trust scopes and re-evaluates every session.
Zero Trust Architecture is a security model, not a product or a vendor. The NIST SP 800-207 definition centers on five operational principles that shift how organizations think about access and trust. Every request for access, from every user and every device, is evaluated continuously, not just at the moment of login.
The five core principles, translated for a non-technical audience:
1. Verify explicitly. Every access request is authenticated and authorized using all available signals: identity, device health, location, and behavior. A user who logged in successfully this morning isn’t automatically trusted this afternoon.
2. Use least-privilege access. Users and systems receive only the minimum access required for their specific task. Access is granted per session, not per employment contract.
3. Assume breach. Architect systems as if an attacker is already inside. This means isolating workloads, encrypting traffic internally, and building detection capabilities that work within the perimeter, not just at the edge.
4. Micro-segment the network. Divide the network into small zones. Even if an attacker compromises one segment, lateral movement to other systems is blocked or slowed significantly.
5. Continuous monitoring and validation. Trust isn’t a one-time decision. It’s re-evaluated on every request, informed by real-time signals.
Traditional Security vs. Zero Trust: A Comparison
| Dimension | Traditional Perimeter Security | Zero Trust Architecture |
|---|---|---|
| Trust model | Implicit inside the network | No implicit trust anywhere |
| Access decision | One-time at login | Continuous, per-request |
| Credential theft impact | High - attacker gains full network access | Limited - access is scoped and monitored |
| Lateral movement | Largely unrestricted inside the perimeter | Blocked by micro-segmentation |
| Remote work fit | Poor - VPN workarounds required | Native - identity-centric, location-agnostic |
| Regulatory alignment | Increasingly out of compliance | Aligned with NIST, OMB, NIS2 |
| Visibility | Limited internal monitoring | Comprehensive logging and behavioral analytics |
For implementation detail on micro-segmentation and service mesh patterns, see Part 3: Technology Deep Dive.
Why 63% Have Started But Only 10% Will Finish
Gartner data captures this gap precisely: 63% of organizations have implemented some form of Zero Trust strategy, yet only 10% of large enterprises will reach a mature, measurable program by 2026. The difference is not technology — it is sustained organizational change management, clear success metrics, and executive sponsorship that outlasts the initial announcement.
The adoption gap is real and has a specific explanation. Gartner’s April 2024 survey found 63% of organizations had implemented a Zero Trust strategy. But a separate Gartner forecast from January 2023 predicted only 10% of large enterprises will reach maturity by 2026. Starting is easy. Finishing is hard.
Several patterns explain why implementations stall.
Scope creep at the start. Organizations often attempt to transform everything at once. ZTA is not a single project. It’s a multi-year program with distinct workstreams across identity, network, data, applications, and endpoints. Teams that try to boil the ocean typically exhaust budget and goodwill before meaningful progress is visible.
Undefined success metrics. Without measurable milestones, boards and CFOs see ongoing expenditure with no clear return. ZTA programs that survive long enough to reach maturity almost always have a clear metrics framework established in the first 90 days.
Fragmented ownership. When Zero Trust sits between the CISO and the CIO with no clear owner, decisions stall. The most successful programs we’ve seen appoint a dedicated ZTA program lead with cross-functional authority and direct executive access.
Vendor lock-in anxiety. The ZTA market is crowded. Organizations paralyzed by platform selection never progress past the evaluation phase. The NIST framework deliberately accommodates multi-vendor environments, which reduces this risk significantly when teams understand it.
63% of organizations worldwide have implemented a Zero Trust strategy as of April 2024, yet only 10% of large enterprises will have a mature, measurable program by 2026. The gap between initiation and maturity is one of the most significant execution risks in enterprise security today. (Gartner, April 2024; Gartner, January 2023)
Why Are Government Mandates Making Zero Trust Compulsory?
OMB Memorandum M-22-09 required all US federal civilian agencies to meet Zero Trust goals by end of FY2024, and the EU NIS2 Directive — effective October 2024 — introduced personal director liability for cybersecurity failures. Any organization in the federal supply chain or serving EU critical-sector customers now faces direct, enforceable compliance obligations, not just best-practice guidance.
Zero Trust is no longer optional for any organization that contracts with government, operates in regulated industries, or does business in the EU. OMB Memorandum M-22-09 required all US federal civilian agencies to meet specific Zero Trust goals by the end of FY2024. CISA published updated implementation guidance in January 2025, reinforcing those requirements and extending the framework’s reach. In January 2026, the NSA followed with the Zero Trust Implementation Guideline Primer — formal NSA-issued guidance for the Department of War (DoW), Defense Industrial Base (DIB), and National Security Systems, mapping 152 ZT activities to a phased Discovery → Target → Advanced rollout model.
The federal mandate has a well-documented private sector ripple effect. Defense contractors, healthcare providers, financial institutions, and any organization in the federal supply chain face contractual obligations that mirror the agency requirements. If your organization sells to the US government, or partners with one that does, ZTA readiness is already a procurement criterion.
EU NIS2 and Personal Director Liability
The EU’s NIS2 Directive, which came into effect in October 2024, introduced something most US executives aren’t yet tracking: personal liability for company directors in the event of significant cybersecurity failures. Under NIS2, senior management can be held individually accountable for decisions that contributed to a breach.
This changes the board conversation. Cybersecurity is no longer a technical concern delegated to the CISO. It’s a governance matter with personal consequences for directors who cannot demonstrate they applied appropriate oversight. Zero Trust, with its emphasis on measurable controls and continuous validation, provides exactly the kind of documented governance posture that satisfies regulatory scrutiny.
OMB Memorandum M-22-09 required all US federal civilian agencies to meet Zero Trust architecture goals by the end of FY2024. CISA released updated implementation guidance in January 2025. The mandate creates direct compliance obligations for federal contractors and supply chain partners, extending Zero Trust requirements deep into the private sector. (WhiteHouse.gov; CISA, January 2025)
What Does a Board-Level ZTA Conversation Look Like?
Organizations with mature Zero Trust programs averaged $3.28M per breach versus the $4.88M global average — a $1.76M per-incident advantage that typically exceeds the full ZTA program cost. The board framing is straightforward: one avoided breach often returns the entire investment, and the ZTA market growing from $17.3B to a forecast $38.5B by 2028 signals this is not a niche bet.
The financial case for Zero Trust is not primarily about implementation costs. It’s about the cost of inaction. Organizations with mature ZTA programs averaged $3.28M per breach, compared to the global average of $4.88M. That’s $1.76M less per incident, according to analysis of the IBM 2024 data. For an organization that experiences even one significant breach, the avoided cost typically exceeds the entire ZTA program investment.
A Forrester Total Economic Impact study commissioned by ThreatLocker in March 2025 found that Zero Trust deployment produced a 184% ROI and $4.15M net present value over three years. This is a vendor-commissioned study and should be weighted accordingly, but the direction of the finding aligns with the IBM breach cost data.
The AI Angle: A New Urgency for 2026
Artificial intelligence adds two dimensions to the ZTA conversation that weren’t present two years ago.
First, AI accelerates attacker capabilities. The WEF Global Cybersecurity Outlook 2025 found that 66% of organizations expect AI to have a major impact on cybersecurity, but only 37% have processes to assess the security of AI tools they’re deploying. Organizations using AI without a Zero Trust foundation are expanding their attack surface faster than they’re securing it.
Second, AI-generated data creates a new governance challenge. Gartner predicts that by 2028, 50% of organizations will adopt Zero Trust data governance in direct response to the proliferation of unverified AI-generated content. When your organization can no longer distinguish human-generated data from AI-generated data at scale, a trust-everything model becomes untenable.
The ZTA market reflects this urgency. The global market for Zero Trust Architecture reached $17.3B in 2023 and is projected to hit $38.5B by 2028, a 17.3% compound annual growth rate. Vendors are investing at this scale because enterprise demand is real and accelerating.
The global Zero Trust Architecture market reached $17.3B in 2023 and is forecast to grow to $38.5B by 2028 at a 17.3% CAGR. This reflects sustained enterprise investment driven by regulatory mandates, breach cost economics, and the expanding AI threat surface. (GlobeNewswire / MarketsandMarkets, November 2024)
Frequently Asked Questions
Is Zero Trust Architecture a product you can buy?
No. Zero Trust is a security strategy and architectural model, not a single product or platform. The NIST SP 800-207 framework accommodates multiple vendors across identity, network, endpoint, and data domains. Organizations that treat it as a procurement decision rather than a program typically land in the adoption gap.
How long does a ZTA implementation take?
Most large enterprises plan for three to five years for a comprehensive ZTA program. Initial quick wins, such as deploying multi-factor authentication and identity governance, are achievable in the first 90 days. Gartner’s forecast that only 10% of large enterprises will have mature programs by 2026 (Gartner, January 2023) reflects how long the full journey takes.
Does Zero Trust apply to small and mid-sized businesses?
Yes, though the scope differs. SMBs can apply Zero Trust principles through identity-centric tools, such as SSO, MFA, and conditional access policies, without enterprise-scale infrastructure. The underlying principle, never grant implicit trust, applies regardless of company size. The breach cost data from IBM 2024 shows that smaller organizations often face proportionally higher damage relative to revenue.
What is the relationship between Zero Trust and cloud security?
Zero Trust and cloud security are complementary. Cloud environments, by nature, dissolve the traditional network perimeter and accelerate the need for identity-centric access controls. Most major cloud platforms include native capabilities that support ZTA principles. Organizations migrating to cloud without a Zero Trust foundation typically inherit significant access risk they don’t immediately see.
How does the EU NIS2 Directive affect non-European companies?
NIS2 applies to any organization providing services to EU member states in covered sectors, regardless of where the organization is headquartered. US, UK, and APAC companies with EU customers in sectors including energy, healthcare, financial services, digital infrastructure, and manufacturing may have direct obligations. Personal director liability under NIS2 applies to management in these organizations.
Q: What is the financial advantage of a mature Zero Trust program compared to no program?
Organizations with mature Zero Trust programs averaged $3.28M per breach versus a $4.88M global average — saving $1.76M per incident, according to IBM 2024 data. For most enterprises, a single avoided breach recovers the full cost of the ZTA program investment, making the financial case straightforward even before factoring in insurance and compliance benefits.
Q: How does AI change the urgency of Zero Trust adoption?
AI accelerates attacker capabilities while simultaneously creating a data governance problem. The WEF Global Cybersecurity Outlook 2025 found 66% of organizations expect AI to have a major cybersecurity impact, yet only 37% have processes to assess the security of AI tools they deploy. Gartner predicts 50% of organizations will adopt Zero Trust data governance by 2028 specifically because AI-generated content undermines trust-everything data models.
Q: What is the size of the Zero Trust market and why does it matter for enterprise decisions?
The global Zero Trust Architecture market reached $17.3B in 2023 and is projected to hit $38.5B by 2028 at a 17.3% CAGR, according to MarketsandMarkets. That scale of sustained vendor investment means robust tooling, competitive pricing, and multi-vendor ecosystem maturity — reducing both implementation risk and vendor lock-in anxiety for organizations starting their ZTA journey today.
Q: What does “assume breach” mean in practice for IT teams?
“Assume breach” means designing systems as if an attacker is already inside the network. Practically, it requires isolating workloads through micro-segmentation, encrypting internal east-west traffic, and building detection capabilities that operate within the perimeter rather than only at the edge. With IBM reporting 292-day average dwell times for undetected credential theft, internal detection is non-negotiable.
Conclusion
Zero Trust Architecture is not a trend that will peak and fade. The economics, the regulatory environment, and the AI-driven expansion of the threat surface all point in one direction. The question for executives in 2026 isn’t whether to adopt ZTA. It’s whether your organization will be among the 10% with a mature, measurable program, or among the 53% that started but stalled.
The $1.76M per-breach cost advantage of mature ZTA programs is a real number, grounded in IBM’s global breach data. The personal director liability introduced by NIS2 is a real risk. The AI-generated data governance challenge that Gartner predicts will drive 50% of organizations toward Zero Trust data governance by 2028 is already arriving.
Start with the adoption gap analysis. Understand where your organization sits on the maturity curve. Then build a program, not a project, around closing it.
Continue with Part 2: The Business Case — PESTEL analysis, ROI data, and board-level justification — or go straight to Part 3: Technology Deep Dive for the implementation roadmap. Organizations running legacy architectures face a harder ZTA adoption path; Application Modernization is often the prerequisite that unlocks full Zero Trust coverage across the portfolio.