The Legacy System Playbook: Four Strategies for Apps That Can't Do Zero Trust
Published
Every 90-day Zero Trust programme hits the same wall in week six: the T0 application that cannot do MFA, cannot speak SAML, cannot participate in conditional access, and cannot be micro-segmented without breaking. Gartner’s 2024 IAM data shows 70% of enterprises maintain legacy apps for 10+ years, and 70% of the Fortune 500 run software built more than 20 years ago. You won’t retrofit Zero Trust into a 1998 mainframe on a 90-day timeline. You will pick one of four strategies and move on.
This is an Operations chapter of the 90-Day Zero Trust Playbook. It cuts across every phase because legacy decisions shape the Chapter P4 device matrix, the P5 baseline, the P6 segmentation design, and the P7 enforcement order.
Key Takeaways
- 70% of enterprises maintain legacy apps 10+ years; 70% of the Fortune 500 run 20+-year-old software (Gartner)
- 60–80% of enterprise IT budget is consumed sustaining legacy systems (enterprise surveys, multiple)
- Each year of delay on a modernisation decision adds ~20–25% to the eventual replacement cost (Deloitte Insights)
- Modernisation, when chosen, delivers 25–35% infrastructure-cost reduction and 40–60% faster releases, with Kyndryl’s 2025 research reporting a 288–362% ROI on completed programmes
- Most legacy T0 systems should not be modernised in 90 days — they should be contained. The 90-day job is picking which of four containment strategies applies
The Four Strategies
Strategy 1 — Wrap (Authentication Proxy)
When it applies. The app has a web interface. It does not speak modern auth (SAML, OIDC). It does handle standard HTTP auth headers, basic auth, or form login.
What you do. Put a reverse-proxy identity gateway in front of it. Cloudflare Access ($7/user/month, free up to 50 users), Zscaler ZPA, Okta Access Gateway, or an open-source option like Pomerium. The gateway handles the Zero Trust concerns — MFA, device posture, conditional access — and passes a signed header to the legacy app, which sees what it expects.
Effort. Days to weeks. The integration is usually deciding which header the legacy app trusts and writing a small policy.
Example. A 2004-era HR system with basic-auth login gets wrapped by Cloudflare Access. The HR team keeps its workflow; the access path now enforces MFA, device trust, and logs every session.
Strategy 2 — Isolate (Network Segmentation + Jump Box)
When it applies. The app has a thick client, speaks a non-HTTP protocol, or otherwise cannot be proxied. Think industrial control systems, older ERP fat clients, mainframe terminal emulation.
What you do. Put the system on its own dedicated network segment. Reach it only through an audited jump host that enforces identity, session recording, and time-bound access. The legacy system does not learn Zero Trust; the boundary does.
Effort. Weeks. The work is network, not application — cooperation with the network team and the system owner, not a code change.
Example. A SCADA system on a plant floor moves to an isolated VLAN. Engineers reach it through a privileged-access jump host with session recording. The SCADA system is blind to the change.
Strategy 3 — Sidecar (Service Mesh Proxy)
When it applies. The app is server-side, handles API traffic, runs in or adjacent to a modern runtime, and cannot natively do mTLS or identity-aware policy.
What you do. Deploy an Envoy or Linkerd-proxy sidecar alongside it. The sidecar handles mTLS, identity, and policy. The app sees unencrypted local traffic on 127.0.0.1, which is what it knows how to handle.
Effort. Medium to high. Requires the app to run in a mesh-capable environment (Kubernetes typically, but also VMs with Consul Connect or similar). Worth it when the alternative is replacing the app.
Example. A Java monolith gets an Envoy sidecar with OPA policy. The monolith keeps its 2011 architecture; the traffic around it enforces 2026 controls.
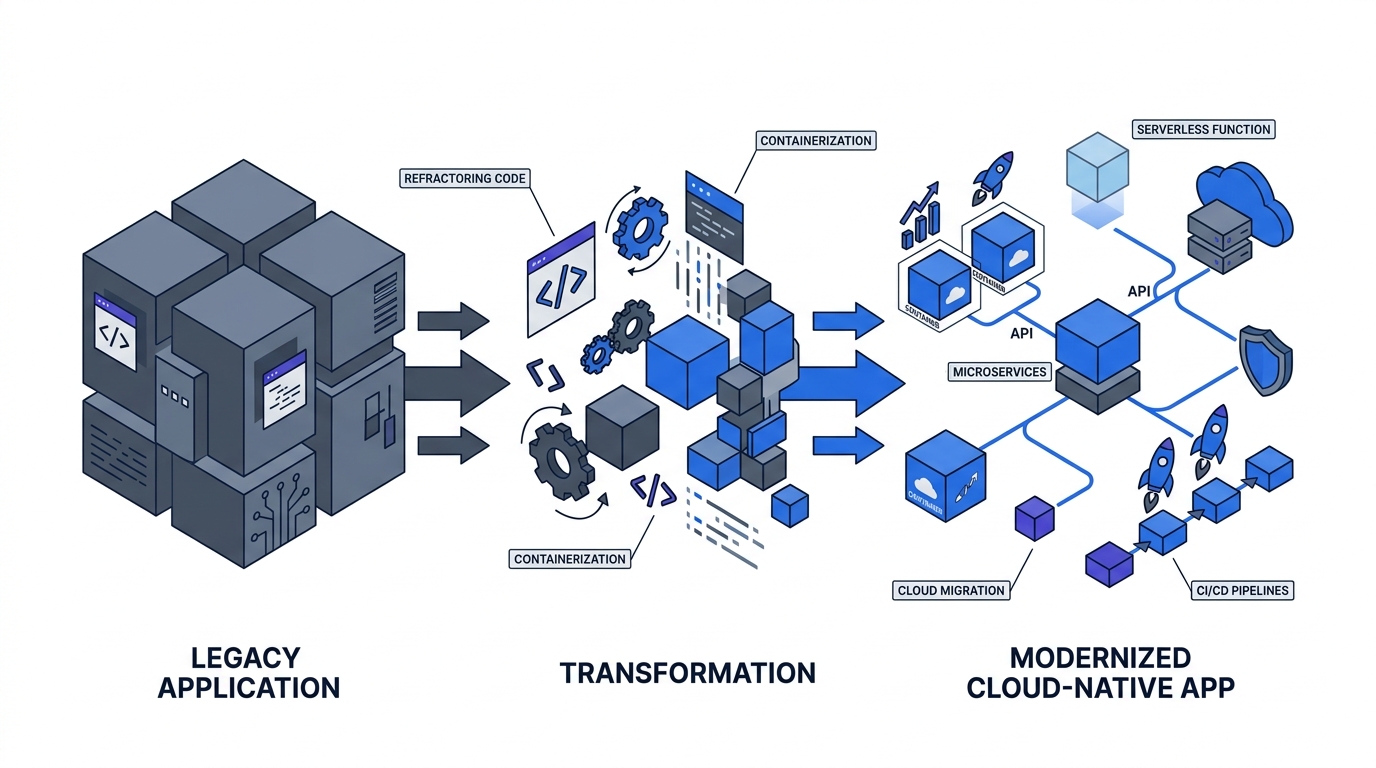
Strategy 4 — Replace (Strategic Retirement)
When it applies. The system is end-of-life, the vendor is out of business, the “wrap” cost is higher than replacement, or the system is a strategic liability beyond security (unmaintainable, unscalable, single point of knowledge failure).
What you do. Write a modernisation plan with a real timeline, real budget, and real executive sponsorship. Everything else is theatre.
Effort. Months to years. Does not fit in a 90-day playbook; appears as a Year-Two line item in the Budget Guide.
Example. A 15-year-old on-prem CRM with vendor support ending gets a two-year roadmap to a cloud CRM. Year 1 is parallel-run and data migration; Year 2 is decommission. The replacement ships modern auth and segmentation native.
The Decision Logic
Pick strategy by answering four questions in order:
- Does it have a web interface that can sit behind a proxy? → Wrap.
- If not, is it server-side and mesh-compatible? → Sidecar.
- If not, is it end-of-life or past its useful life? → Replace (and Isolate until replacement lands).
- Otherwise → Isolate.
Isolate is the default answer for everything that doesn’t fit another strategy. It is not a failure state — it is the boundary control that buys time for the real decision (replace) without leaving the system unprotected.
The Cost of Waiting
Deloitte’s modernisation research and practitioner write-ups converge on a 20–25% annual cost escalation for legacy decisions deferred. The reasons: vendor support premiums, dwindling engineering talent familiar with the stack, compounding integration debt, and the widening gap between the legacy platform’s security model and what the rest of the estate expects.
Kyndryl’s 2025 mainframe modernisation research reports completed programmes delivering 25–35% infrastructure cost reduction, 40–60% faster release cadence, and 288–362% ROI over a multi-year horizon. The business case for Replace is usually easier to write than it looks — what’s hard is the organisational commitment to a 24-month project when the current budget cycle is 12.
What Lives in the Playbook Artifact
For each T0 and T1 legacy system, the playbook artifact captures:
- System name, owner, criticality tier
- Chosen strategy (wrap / isolate / sidecar / replace)
- Compensating controls in place while the strategy is being executed
- Target completion date
- Re-evaluation date (quarterly for Isolate; yearly for Replace)
This document is the single biggest protection against legacy systems silently graduating from “temporary exception” to “permanent bypass.” Review it at the Governance Structure steering committee every quarter.
Return to the 90-Day Playbook hub for the rest of the cross-cutting operations chapters.


