Zero Trust Budgeting: What It Actually Costs
Published
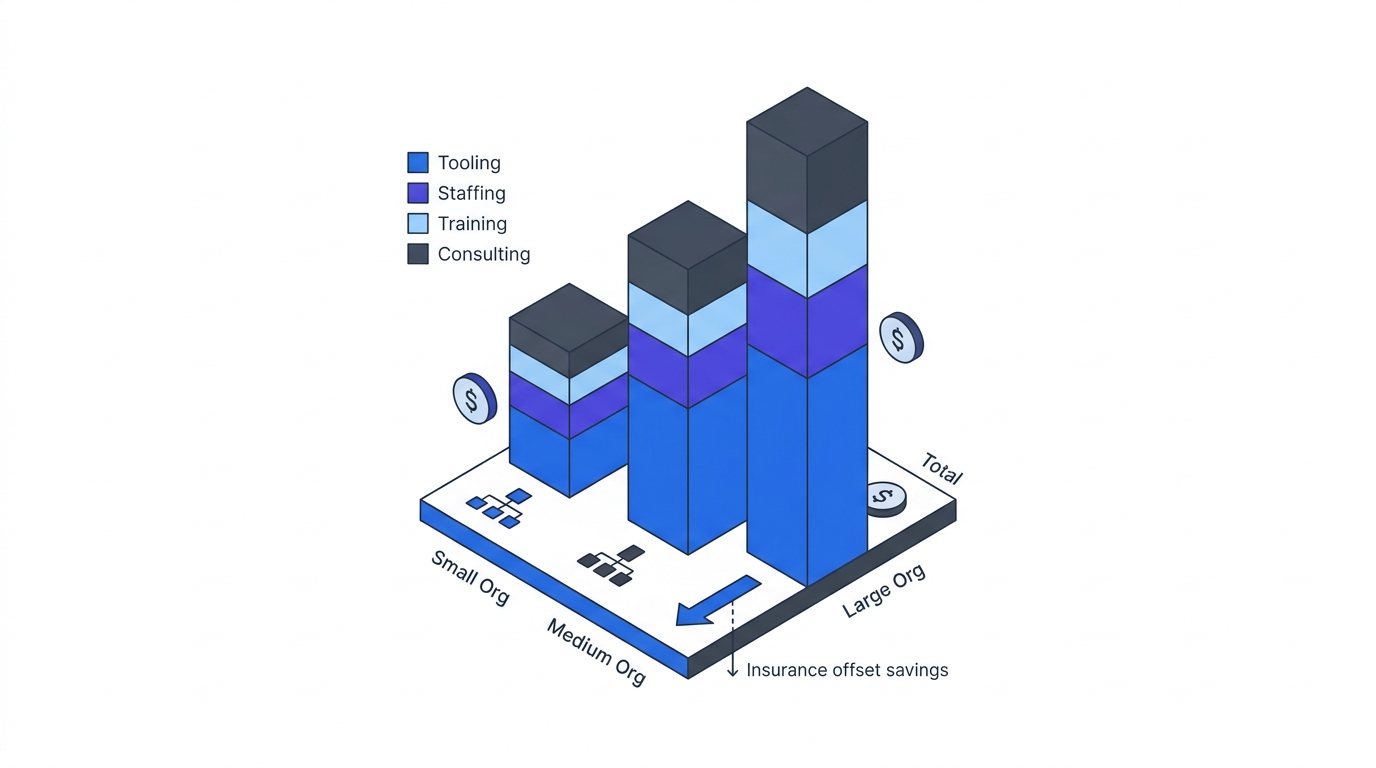
Budget conversations are where Zero Trust programmes get lost. The CFO asks “what does this cost?” and the answer is either a vendor-quoted number that understates total cost of ownership by an order of magnitude, or a vague “it depends” that signals the team hasn’t done the math. This chapter is the math. Licence pricing, staffing costs, training spend, and the insurance offset — the numbers that let a CTO present a defensible budget to the board.
This is an Operations chapter of the 90-Day Zero Trust Playbook. It pairs with the Measurement Dashboard for the full “what it costs and what it delivers” pair that the board needs.
Key Takeaways
- Typical 90-day foundation cost: $1.4M–$2.1M for a mid-market enterprise (~$200M revenue, 500–2,000 employees). Year Two expansion: $800K–$1.2M
- Tooling is rarely the cost overrun. Labour and integration are. ISC² reports 90% of security orgs report skills gaps, 27% cite Zero Trust specifically, and 40% of security roles take 6+ months to fill
- Cyber insurance offset is real: 20–50% premium reduction with core controls deployed, and 75% of insurers now assess segmentation maturity in underwriting. S&P forecasts 15–20% premium increases in 2026 for organisations without them
- Forrester’s Total Economic Impact study pins Zero Trust ROI at 111% with a 5-month payback; IBM’s 2025 data adds $1.9M per-breach savings for AI-enabled security ops
- When to hire vs. consult: identity/IAM = always bring expertise in; architecture = usually; segmentation = sometimes; ongoing operations = rarely outsource
Vendor Pricing by Category
Published pricing, mid-market volume. Adjust for your contract leverage. All monthly unless noted.
Identity Provider
- Microsoft Entra ID — $6–9/user, or bundled in M365 E3/E5 (most enterprises already own this)
- Okta — $6–17/user depending on tier
- Ping Identity — enterprise pricing, typically $4–10/user
- Keycloak — open source, self-hosted
EDR (Endpoint Detection & Response)
- CrowdStrike Falcon — $5–15/device depending on module mix
- Microsoft Defender for Endpoint — bundled in M365 E5, ~$10/user add-on for E3
- SentinelOne — $5–6/endpoint
- Wazuh — open source
ZTNA (Zero Trust Network Access)
- Cloudflare Access — $7/user, free up to 50 users
- Zscaler Private Access — $6–10/user
- Tailscale — $6/user, free tier
- Twingate — $10–18/user depending on tier
MDM (Mobile / Device Management)
- Microsoft Intune — ~$8/user, bundled in most M365 plans
- Jamf Pro — $4–20/device depending on tier
- Kandji — $4/device
- JumpCloud — $7–18/device bundled with identity
Segmentation
- Illumio — $10K–15K+/year depending on scope
- VMware NSX — enterprise pricing, typically per-vNIC
- Cilium — open source (free); Isovalent enterprise support ~$20K+/year
- Cloud-native security groups (AWS/Azure/GCP) — free, you already pay for them
Secrets Management
- HashiCorp Vault OSS — free, self-hosted
- Vault Enterprise — ~$100K+/year
- AWS Secrets Manager / Azure Key Vault — consumption-based, usually <$5K/year mid-market
- Doppler / Infisical — $8–15/user for the small-team tier
For a mid-market org, bundled M365 E5 + CrowdStrike + Cloudflare Access covers 80% of the Zero Trust tooling surface at roughly $40–55/user/month all-in. Segmentation, secrets, and PAM add on top.
Staffing Reality
Salary bands (US, 2025):
- Zero Trust Architect — $91K–$216K, median $114K
- IAM Engineer — $84K–$132K
- Security Engineer — $143K–$159K
Team size by org size:
- 200–500 employees — 1 dedicated programme lead. Identity and network work done by existing IT/security staff with 30–50% allocation.
- 2,000–10,000 employees — 4–6 dedicated. Architect, two identity engineers, one segmentation engineer, one programme manager, plus rotational operations support.
- 10,000+ employees — 6–10+ dedicated, plus regional leads. Architecture becomes a full team, not a role.
The Skills Gap Is the Schedule Risk
ISC²’s 2024 Cybersecurity Workforce Study puts 90% of security organisations reporting skills gaps. ISACA’s State of Cybersecurity data attributes 55% of security teams to being understaffed, with 40% of open roles taking 6+ months to fill. 27% of respondents cite Zero Trust specifically as a skills shortfall.
The practical implication: the 90-day timeline assumes the people are already in seats. If you are hiring into the programme, add a quarter to the timeline before Phase 1 can start. Alternatively, bring in consulting capacity for the first phase while building internal capability in parallel.
Training Spend
Surprisingly modest relative to the tooling line:
- ISC² Zero Trust Certificate — 9 hours, ~$80. Good baseline for the whole team.
- SANS SEC530: Defensible Security Architecture — 6-day course, ~$8,000/seat. The deep one for architects.
- CISA Zero Trust Maturity Model training — free. Every team member should work through this.
- NSA Zero Trust Implementation Guideline Primer (January 2026) — free, published via CSA. 152 activities across 42 capabilities, mapped into four phases. The single best document for sizing the multi-year scope of work to a CFO who thinks Zero Trust is a quarterly tooling project.
- Vendor certifications — Okta Certified Professional, CrowdStrike Certified Falcon Responder, etc. ~$300–$1,500 per cert. Fund for the operators.
Total training budget for a mid-market programme: ~$25K–$50K. This is the cheapest line item on the page and consistently the first one CFOs try to cut. Resist.
When to Hire vs. Consult
- Identity / IAM — always bring expertise in. The Entra/Okta/PingFederate configuration choices made in the first six weeks shape the next five years.
- Architecture — usually bring in a Zero Trust architect for the first 90 days. Hand off to internal staff by end of Phase 3.
- Segmentation — sometimes. If the estate is K8s-native with a strong platform team, internal is fine. Brownfield hybrid estates usually need vendor professional services for the first rollout.
- Ongoing operations — rarely outsource. Operations needs institutional knowledge of which exceptions exist, which legacy systems matter, and which users matter. That lives inside, not with a consultant.
Cyber Insurance Offset
Zero Networks’ 2024 research reports 20–50% premium reduction for organisations with core Zero Trust controls (MFA, segmentation, EDR) deployed. 75% of insurers now assess segmentation maturity explicitly in underwriting — up from roughly 0% five years ago.
The counterfactual matters: S&P Global forecasts cyber insurance premium increases of 15–20% in 2026 for organisations without mature controls. So the offset is not “flat vs. 20% discount”; it is “20% increase vs. 20% decrease” — a 40-point swing at premium-renewal time.
For a mid-market org with a ~$500K annual cyber insurance premium, the controls deployed in this playbook are worth $100K–$250K/year in offset alone. That is typically enough to justify 0.5–1 FTE of dedicated programme staff on the insurance-offset line by itself.
ROI Framing for the Board
Three numbers, all sourced, for the board conversation:
- Forrester TEI: 111% ROI, 5-month payback on a representative Zero Trust deployment.
- IBM 2025: $1.9M per-breach savings for organisations with AI-enabled security operations — applicable to the anomaly-detection and automated-containment components.
- Insurance offset: 20–50% premium reduction with core controls, translating to $100K–$500K annually for mid-market and seven-figures for large enterprise.
Combine with the Measurement Dashboard financial framing and the budget defends itself without a vendor deck.
What the Artifact Delivers
By the end of this chapter, you should have:
- A three-year budget model covering tooling, staffing, training, and consulting by category and phase
- A hiring plan aligned to the programme timeline, with gap-filling consulting contracts for Phase 1
- A documented insurance-offset conversation with the broker before Day 90
- A board-ready ROI framing with three sourced reference points
- A Year-Two expansion budget with the specific tooling and staffing lines that extend past the foundation
Return to the 90-Day Playbook hub to review the full 15-chapter sequence end to end.