The Axios npm Compromise: Why Zero Trust Is a Blast-Radius Control, Not a Prevention Control
Published
For about three hours on the morning of 31 March 2026, two compromised versions of the axios HTTP client — axios 1.14.1 and axios 0.30.4 — were live on the npm registry. Both were published from a compromised maintainer account. Both pulled in a phantom dependency called plain-crypto-js 4.2.1 whose only real purpose was to run at install time and drop a cross-platform remote access trojan on Windows, Linux, and macOS machines that installed them (axios post-mortem; Microsoft Security Blog, April 2026; GitHub Advisory GHSA-fw8c-xr5c-95f9).
The compromise window was short. The blast radius was not. Axios is one of the most widely used HTTP clients in the JavaScript ecosystem — reported weekly download volumes for affected lines range between 70 and 100 million (Microsoft, April 2026; Google Cloud Threat Intelligence, April 2026). Any developer workstation, CI runner, or build server that performed a fresh install inside the exposure window is, according to the official GitHub advisory, to be treated as fully compromised.
This is a case study on two questions that should matter to every CTO and every IT architect responsible for a build plane in 2026:
- What actually happened, in enough detail that your team can check whether you were exposed?
- Where does Zero Trust Architecture fit — and, just as important, where does it not?
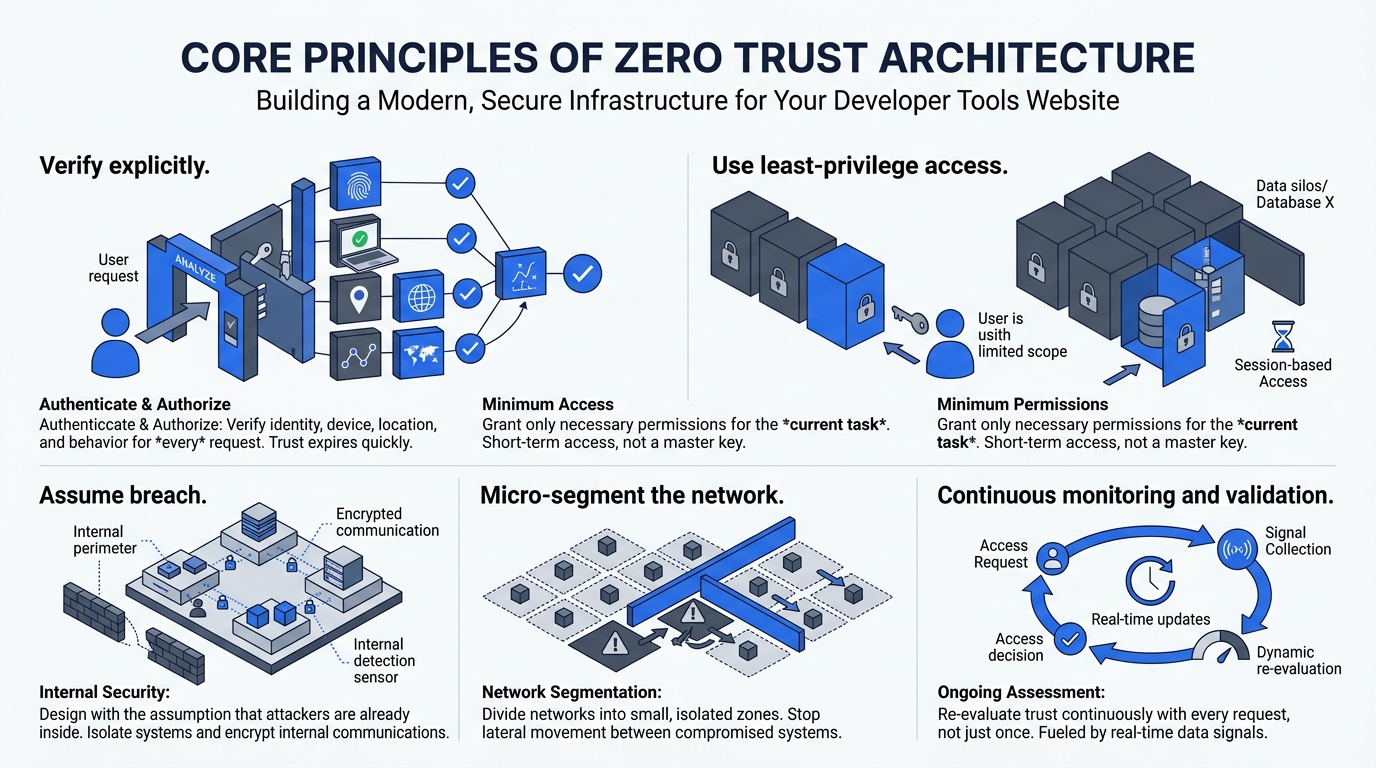
For the fundamentals of Zero Trust, see the Zero Trust Architecture executive guide. This post assumes familiarity with the NIST SP 800-207 model and focuses on its role in supply-chain compromise containment specifically.
Key Takeaways
- Two axios versions (1.14.1 and 0.30.4) were published with an injected malicious dependency during a ~3-hour window on 31 March 2026 (axios post-mortem)
- The compromise was a manifest-only change — axios source code was untouched. The attacker added a phantom dependency whose
postinstallscript dropped a RAT (StepSecurity, April 2026)- Microsoft attributes the operation to “Sapphire Sleet”; Google attributes to UNC1069 — both a North Korea–nexus actor set (Microsoft, April 2026; Google Cloud, April 2026)
- Zero Trust Architecture does not prevent a malicious upstream package from being published. It materially reduces the downstream impact once a developer endpoint or CI runner is compromised — by constraining credential access, lateral movement, and production reach (NIST SP 800-207)
- Any machine that installed the malicious versions should be treated as fully compromised and rebuilt, not cleaned in place (GitHub Advisory GHSA-fw8c-xr5c-95f9)
What Actually Happened
The immediate cause was unauthorised package publication using the lead maintainer’s compromised publishing capability. According to the axios maintainer’s public post-mortem, a targeted social-engineering campaign roughly two weeks before the incident led to a RAT infection on the maintainer’s personal machine, which then enabled theft and use of npm publishing credentials (axios post-mortem).
The attacker did not need to alter axios source files. Instead, they injected a new runtime dependency into package.json so that npm install would pull and execute a malicious package during the install phase. StepSecurity’s published diff shows that package.json was essentially the only substantive change in the compromised releases, and the injected dependency was never imported anywhere in axios’ actual code — a classic “phantom dependency” (StepSecurity, April 2026).
That injected dependency was plain-crypto-js 4.2.1, deliberately named to evoke the well-known crypto-js package. It contained a postinstall lifecycle script that ran node setup.js on installation — the primary execution vector. Both Microsoft and Google’s threat-intelligence analyses describe a stage-1 obfuscated JavaScript loader that pivoted to OS-appropriate stage-2 delivery using curl from a command-and-control server (Microsoft, April 2026; Google Cloud, April 2026).
Timeline (UTC)
| Time | Event | Source |
|---|---|---|
| Mid-March 2026 | Targeted social engineering campaign begins against the lead maintainer | axios post-mortem |
| 30 Mar, 05:57 | plain-crypto-js 4.2.0 published as a benign “seed” release | axios post-mortem |
| 31 Mar, 00:21 | axios 1.14.1 published with malicious dependency injection | axios post-mortem; Microsoft |
| 31 Mar, ~01:00 | axios 0.30.4 (legacy line) published with the same injection | axios post-mortem; Elastic |
| 31 Mar, 01:38 | Collaborator PR opened to deprecate; direct contact with npm | axios post-mortem |
| 31 Mar, 03:15 | Malicious axios versions removed from npm | axios post-mortem |
| 31 Mar, 03:20 | Google’s observed end of the malicious window | Google Cloud |
| 31 Mar, 03:29 | plain-crypto-js removed from npm | axios post-mortem |
| 1 Apr | Coordinated vendor advisories and IOC publication | Microsoft; Elastic; Wiz |
The practical exposure heuristic from the maintainer: any system that performed a fresh install between 00:21 and roughly 03:15 UTC on 31 March 2026, and resolved to the malicious versions, is at risk (axios post-mortem).
Why This Is Different From a Normal CVE
This is not a vulnerability in the classical sense. There is no bad memcpy, no injection flaw in the axios library itself, no line of code to patch. The affected versions contained embedded malicious code. The GitHub Advisory Database is unambiguous: affected machines must be treated as fully compromised, and there is no guarantee that uninstalling the package removes all malicious effects (GitHub Advisory GHSA-fw8c-xr5c-95f9).
Two widely used, entirely legitimate features of the JavaScript ecosystem were turned into attack surface:
Dependency-graph execution. The JavaScript resolver does exactly what you tell it to do. A dependency added to package.json is pulled and installed. No code review happened between the maintainer commit and a developer’s laptop.
Lifecycle scripts (postinstall). npm runs install-time scripts by default. This is convenient for legitimate packages that need to compile native modules or run setup code. In this case, it was the execution vector for dropping a cross-platform RAT. Disabling lifecycle scripts globally (npm install --ignore-scripts) would have blocked the payload, but many legitimate packages depend on them — so disabling them requires organisational policy and targeted exception handling (Microsoft, April 2026).
A third amplifier was cultural: semver range operators (^ and ~) in package.json allow automatic uptake of patch and minor releases. Microsoft’s incident guidance recommends removing caret and tilde ranges for contexts that require human review of updates, precisely because they enable silent auto-upgrade to a malicious patch release (Microsoft, April 2026).
What the RAT Actually Did
Multiple independent analyses — from Microsoft, Google, Elastic Security Labs, Wiz, and Socket — describe consistent capabilities in the stage-2 payload:
- Host inventory and OS fingerprinting (via
POSTto C2) - Periodic beaconing to the command-and-control server
- Remote command execution
- File-system enumeration
- Persistence mechanisms (e.g. Windows registry Run keys, dedicated persistence scripts)
- Anti-forensic cleanup: self-deletion of the dropper and swapping
package.jsonwith a benignpackage.mdso the installednode_modulesdirectory looks clean after execution (Elastic Security Labs; Wiz; Socket)
This capability set makes credential theft and follow-on environment compromise the realistic risk — especially on developer endpoints and CI runners, where cloud API keys, signing tokens, and publishing tokens tend to live. Google’s advisory explicitly warns that stolen secrets from recent supply-chain incidents can enable downstream compromise of source control, container registries, cloud accounts, SaaS admin planes, and ultimately customer environments (Google Cloud, April 2026).
High-Value Indicators of Compromise
| Indicator type | What to look for |
|---|---|
| Package versions | axios@1.14.1 or axios@0.30.4 present in lockfiles or build logs |
| Dependency presence | node_modules/plain-crypto-js/ directory at all (it is not a legitimate axios dependency) |
| Dropper script | Install-time execution of setup.js |
| Network IOCs | Outbound traffic to sfrclak.com:8000 / 142.11.206.73 / path /6202033 |
| macOS artifact | /Library/Caches/com.apple.act.mond |
| Windows artifacts | %PROGRAMDATA%\wt.exe, %TEMP%\6202033.ps1, %TEMP%\6202033.vbs, system.bat |
| Linux artifact | /tmp/ld.py |
| Anti-forensics swap | Presence of package.md in compromised node_modules folders |
Sources corroborate these across Microsoft’s incident analysis, Elastic Security Labs, Wiz, and the GitHub advisory. IOCs may age out — network endpoints are likely sinkholed by the time you read this — but file-system artifacts remain useful for retrospective hunting (Microsoft, April 2026; Elastic; Wiz).
Immediate Remediation (the 24-Hour Playbook)
These steps synthesise the maintainer’s guidance, government advisories, and vendor incident-response recommendations.
Containment threshold. If you find evidence of affected axios versions or plain-crypto-js, isolate the host, treat it as compromised, and assume credentials used on that machine are compromised (GitHub Advisory; CSA Singapore Advisory AD-2026-002).
Package-level rollback. Roll back to known-good versions — commonly cited: axios 1.14.0 for the 1.x line and axios 0.30.3 for the 0.x line — and remove plain-crypto-js from node_modules across all environments (Microsoft, April 2026).
Credential and secret rotation. Rotate every secret that was present on or injected into affected machines — API keys, tokens, SSH keys, CI secrets — and perform rotations from a known-good system, not the compromised one. The maintainer, GitHub’s malware advisory, and multiple government CERTs all emphasise this (axios post-mortem; GitHub Advisory).
CI/CD runner actions. If a CI runner performed installs during the exposure window, its image and secret store should be treated as compromised. Rebuild runner images and rotate any secrets injected into them.
Cache and artifact hygiene. Clear package-manager caches and internal artifact proxies. Cached tarballs can extend exposure well beyond registry takedown — npm cache clean --force is explicitly recommended in Microsoft’s incident guidance.
Do not clean in place. Where doubt exists, rebuild rather than scrub. This is a repeated recommendation across vendor and advisory sources and reflects the assumption that a RAT with persistence may have modified other system components.
Long-Term Mitigations
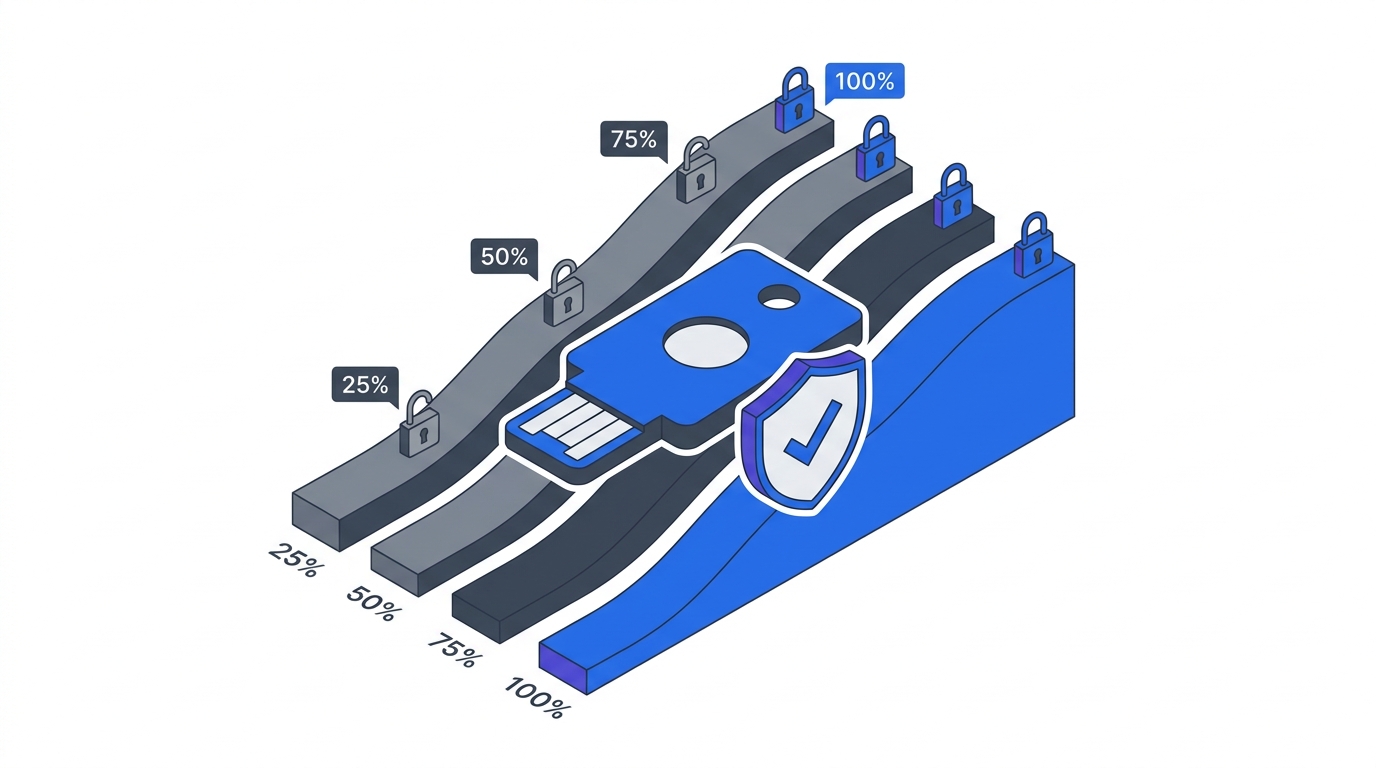
The axios compromise should drive decisions across two loops: a prevention loop (make it harder for a compromised package to reach your pipeline at all) and a containment loop (make the blast radius smaller when it does). Zero Trust belongs squarely in the second loop.
Prevention-Loop Controls
| Control | What it does | Strength against this attack class |
|---|---|---|
Exact version pinning for critical deps (no ^/~) | Blocks silent auto-uptake of malicious patch releases | High |
Deterministic installs (npm ci + lockfile discipline) | Ensures installs match reviewed lockfiles | High, if lockfiles are controlled |
| Dependency “age gate” / quarantine on new packages | Blocks freshly published packages and versions by default | Medium–high |
| Private registry proxy + allowlist | Central checkpoint before public packages reach dev/CI | High in enterprises |
--ignore-scripts for high-risk contexts | Prevents postinstall execution | High for install-time malware specifically |
| Provenance verification + signing (npm provenance, OIDC trusted publishing) | Ensures only expected pipelines can publish | High against “stolen credential publish” scenarios |
The npm ecosystem has made real progress here. npm provenance statements and npm trusted publishers let package consumers verify that an artefact came from an expected build pipeline rather than a developer’s laptop. Axios committers have since stated they are moving toward immutable releases and stronger publish controls — a direct reaction to the incident (axios post-mortem).
Containment-Loop Controls (Where Zero Trust Lives)
NIST SP 800-207 defines Zero Trust as minimising uncertainty in least-privilege, per-request access decisions “in the face of a network viewed as compromised” — shifting emphasis from perimeter trust to resource-focused enforcement (NIST SP 800-207). That framing maps cleanly onto modern supply-chain reality: compromise may originate inside trusted developer and CI planes.
ZTA does not stop a malicious upstream package from being published or installed. That problem belongs to the prevention loop — registry controls, provenance, policy gates. Any vendor or consultant telling you “Zero Trust would have prevented the axios incident” is selling the wrong story.
ZTA does materially reduce the blast radius once a developer endpoint or CI runner is compromised. The downstream harms from axios are credential theft, lateral movement, and unauthorised access to production systems and customer data. ZTA addresses all three:
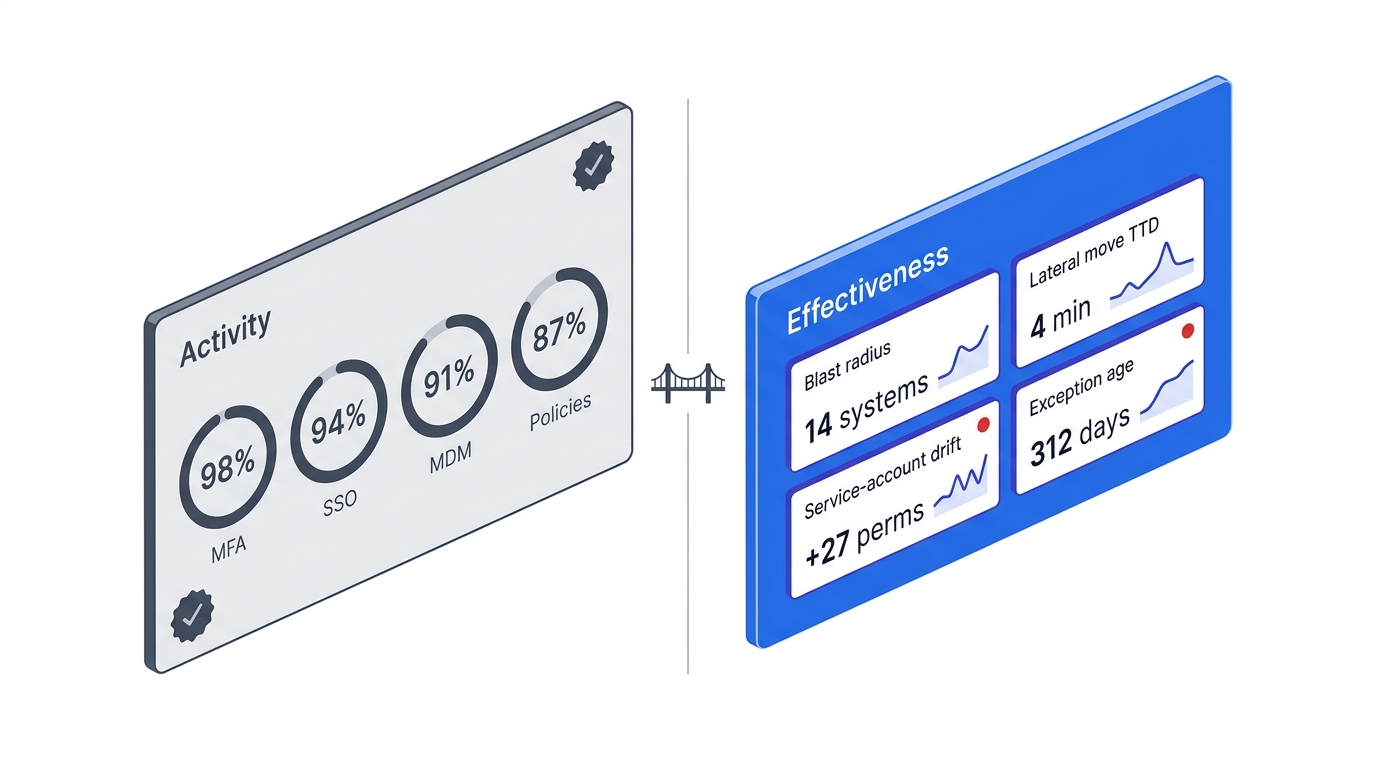
- Strong identity and device posture checks. A compromised developer laptop should lose access to sensitive repos and cloud accounts until reimaged — not after a scheduled review.
- Granular authorisation close to resources. Policy enforcement points should evaluate every request against the live state of the asking workload, not against a VPN session started hours ago.
- Continuous evaluation, not implicit trust. CI runners should be untrusted workloads that earn access per job via short-lived identity, not long-lived credentials stored in a secret manager.
Applied to this incident specifically:
- Zero Trust for CI/CD runners means treating every runner as untrusted, using workload identity (e.g. OIDC federation to cloud providers), and denying access to most secrets by default.
- Micro-segmentation of build systems means build networks are isolated, egress is restricted to known endpoints, and all dependency retrieval flows through controlled proxies — directly breaking the outbound HTTP pattern that the stage-2 payload relied on.
- Device trust for developer endpoints means a compromised developer machine loses access to production-adjacent resources automatically, not when someone reviews the SOC ticket.
For the full NIST framing and where these controls sit in the broader Zero Trust model, see the ZTA technology deep dive. For the business case for investing in Zero Trust ahead of the next incident, see the ZTA business case.
Regulatory Exposure
Supply-chain compromises increasingly intersect with hard regulatory duties, not just best-practice guidance.
GDPR Article 32 requires “appropriate technical and organisational measures” proportionate to risk where personal data is processed — shaping both prevention expectations and post-incident scrutiny of whether access control, logging, and resilience measures were appropriate (GDPR Art. 32).
SEC cybersecurity disclosure rules (adopted 2023) require US public companies to disclose material cybersecurity incidents on Form 8-K Item 1.05 within four business days of a materiality determination. Supply-chain compromise is squarely in scope if business impact or customer harm is material (SEC 2023-139).
EU NIS2 Directive entered into force in January 2023 with Member State transposition required by October 2024, expanding scope and cyber-risk management and reporting duties for organisations in critical sectors (European Commission).
Organisations in scope of any of these should clarify materiality thresholds and escalation paths for supply-chain compromise specifically — not just for “classic” CVE-style vulnerabilities. The triage question in an incident like axios is not “is this CVE exploited in the wild?” but “which of our machines ran npm install during the exposure window, and what did those machines have access to?”
Two Audiences, Two Decisions
For CTOs and engineering leadership, the axios compromise is a case study in trust being transitive — and so are its failures. A human maintainer endpoint compromise became an ecosystem-wide distribution channel in hours. The decisions that matter at your level are not technical — they are about whether your build plane has been designed with “assume breach” in mind. Are CI runners ephemeral? Are secrets short-lived? Is there a single registry checkpoint where dependency policy can be enforced? Does your organisation have a materiality playbook for supply-chain compromise, or will the first such incident be the one where you figure it out?
For IT architects and platform engineers, the actionable themes are three: detect manifest-only compromise via dependency diff gates, treat install-time execution as a discrete control point (scripts, egress, sandboxing), and minimise the secret footprint of CI runners and developer endpoints, because the RAT’s value is secrets and remote access, not the compromised library’s functionality. Axios happened to be the vehicle this time. The design decisions you make should not depend on the vehicle.
The uncomfortable truth both audiences should internalise: the next incident is already in draft somewhere. The question is whether it will be three hours of cleanup or three months of downstream compromise. That difference is architecture.
Further Reading on BizTechBridge
- Zero Trust Architecture: The Executive Guide for 2026 — what ZTA actually means and why it is moving from best practice to regulatory expectation
- Zero Trust Business Impact — the financial case, breach-cost differentials, and board-level framing
- Zero Trust Technology Deep Dive — implementation patterns across identity, network, and data
Connect on LinkedIn for weekly analysis on security, platform engineering, and application modernisation.