The Application Criticality Scorecard: Prioritizing Your Zero Trust Rollout
Published
The #1 Reason Zero Trust Programs Fail: Scope Creep
Your organization has 500 applications. Your CEO wants them all secured by Q3. Your team has eight engineers. The math doesn’t work — and every Zero Trust program that ignores it burns out by month four.
The most successful Zero Trust architecture (ZTA) deployments don’t try to secure everything at once. They ruthlessly prioritize. They identify which 10–15% of applications account for 90% of business risk, and they ship those first. The rest follow in waves.
This article walks you through the Application Criticality Scorecard — a three-axis scoring model that CTOs have used to:
- Cut evaluation time from weeks to days
- Get board buy-in on phased rollouts (instead of the “secure everything now” fantasy)
- Identify which apps need wrapping strategies before attempting direct hardening
- Build a roadmap with clear, defensible milestones
This is the first artifact you create before Day 1 of Zero Trust.
The Three-Axis Scoring Model
Rate every application on three independent dimensions, each on a scale of 1–5.
1. Business Impact (1–5)
How much does your business depend on this application?
- 5 — Revenue-generating or mission-critical (payment processing, order management, customer-facing platform). Downtime = immediate financial loss.
- 4 — High operational importance (email, CRM, ERP core modules). Downtime disrupts dozens of users.
- 3 — Moderate importance (departmental tools, analytics platforms). Downtime affects one team.
- 2 — Limited scope (legacy HR system used by payroll only). Downtime impacts small group.
- 1 — Nice-to-have or soon-to-sunset. Business survives without it.
2. Data Sensitivity (1–5)
What data does this application handle?
- 5 — Highly regulated PII (credit cards, SSNs, health records). GDPR/HIPAA/PCI compliance required. Breach = fines + litigation.
- 4 — Sensitive internal data (employee records, financial statements, proprietary IP). Breach = competitive harm.
- 3 — Mixed data (departmental records, non-sensitive customer info). Breach = reputation damage.
- 2 — Mostly public or low-value data. Breach = minor embarrassment.
- 1 — No sensitive data. Public-facing read-only tools.
3. Technical Feasibility (1–5)
Can this application actually support modern identity and access controls?
- 5 — Cloud-native, SaaS, SAML/OIDC-ready. Native integration path.
- 4 — Cloud or on-prem with API layer and directory integration. 4–6 week implementation.
- 3 — Legacy architecture with API support, but no SAML. Requires LDAP bridge or reverse proxy. 8–12 weeks.
- 2 — Monolithic, LDAP-only, limited API. Requires application wrapper. 12–16 weeks or accept risk.
- 1 — Proprietary authentication, no API, vendor won’t support standards. Wrapping + isolation only.
Tier Categorization: The Roadmap
Add the three scores. Total = 3–15 combined score.
| Tier | Score Range | Meaning | Action |
|---|---|---|---|
| Tier 1: Mission-Critical | 12–15 | High business impact + sensitivity. Must be secured first. | Phase 1: 90 days. May need wrapping if feasibility is low (3–4). |
| Tier 2: Important | 8–11 | Significant impact or sensitivity. Secure in Phase 2. | Phase 2: 90–180 days. Accept 4–6 week implementations. |
| Tier 3: Low-Risk | 4–7 | Limited impact and low data sensitivity. Phase 3 or accept risk. | Phase 3: 180+ days. Can defer if resources are constrained. |
| Tier 4: Sunsetting | Any score, if EOL within 12 months | Not worth hardening. Isolate and wrap only. | Accept risk or sunsetting gate: block new access, scheduled decommission. |
Worked Example: Enterprise Portfolio
Here’s how a typical mid-market organization scores:
| Application | Business Impact | Data Sensitivity | Feasibility | Total | Tier | Phase 1 Status |
|---|---|---|---|---|---|---|
| SAP ERP | 5 (mission-critical financials) | 5 (GL, AP/AR, payroll) | 3 (legacy, no native OIDC) | 13 | Tier 1 | ✓ Prioritize. Plan 12-week wrapping strategy. |
| Salesforce CRM | 4 (revenue-critical) | 4 (customer contact, contracts) | 5 (native SAML/SSO) | 13 | Tier 1 | ✓ High-feasibility target. Week 2–3. |
| Microsoft 365 Email | 4 (operational backbone) | 3 (internal comms, some PII) | 5 (Entra ID native) | 12 | Tier 1 | ✓ Prerequisite. Week 1 (often already gated). |
| Workday HR | 3 (departmental) | 4 (employee PII, SSNs) | 5 (native SAML) | 12 | Tier 1 | ✓ Week 4–5. High sensitivity, easy integration. |
| Legacy HR System (EOL 2026) | 3 (used by payroll team) | 4 (salary data, W-4s) | 1 (COBOL, no API) | 8 | Tier 2 | ✗ Accept risk. Plan decommission instead. |
| Internal Developer Tools | 2 (developers only) | 1 (no sensitive data) | 5 (REST API, OAuth-ready) | 8 | Tier 2 | — Quick win. Phase 2, low risk. |
| Custom Reporting Dashboard | 1 (BI team reads data) | 2 (aggregated, anonymized) | 4 (web app, can add reverse proxy) | 7 | Tier 3 | — Defer or accept. Phase 3. |
| External Customer Portal | 2 (low revenue dependency) | 2 (basic account info only) | 3 (third-party SaaS, limited integration) | 7 | Tier 3 | — Defer. Phase 3. |
Real timeline for this portfolio:
- Phase 1 (90 days): Microsoft 365, Salesforce, Workday → ~40% of ZTA adoption.
- SAP wrapping strategy: Parallel work, 12 weeks. Not blocking Phase 1, but planned.
- Phase 2 (180 days): Developer tools, customer portal → incremental hardening.
- Legacy HR system: Scheduled for decommission Q4 2026. Accept risk in the interim.
Inventory Timeline Expectations
How long does application discovery and scoring take?
| Organization Size | Typical App Count | Timeline | Method |
|---|---|---|---|
| Small (<100 apps) | 50–100 | 2–3 weeks | Manual discovery + interviews |
| Mid-market (500–1K apps) | 500–1,000 | 4–6 weeks | Active Directory, firewall logs + spot checks |
| Enterprise (5K+ apps) | 5,000–10,000+ | 4–8 weeks | Automated CMDB discovery + LeanIX or ServiceNow assessment |
Tip: Don’t wait for 100% accuracy. Score the top 200 applications first (usually 80% of your risk). Assign Tier 4 to unknowns. Phase 1 doesn’t depend on finding every orphaned app.
The 2×2 Prioritization Matrix
Plot your Tier 1 and Tier 2 applications on two axes:
- X-axis: Technical Feasibility (1–5, left to right)
- Y-axis: Business Impact (1–5, bottom to top)
This creates four quadrants:
-
Top-Right (High Impact, High Feasibility) — “Phase 1 Targets”
Salesforce, Workday, Microsoft 365. Ship first. These unlock fast wins and prove the program works. -
Top-Left (High Impact, Low Feasibility) — “Wrap or Isolate”
SAP, legacy mainframe apps. High value, high effort. Parallel work stream: design wrapping strategy (reverse proxy, adapter layer, segmentation). -
Bottom-Right (Low Impact, High Feasibility) — “Quick Wins”
Internal tools, dashboards, developer platforms. Easy to harden. Great for momentum and team morale. Phase 2. -
Bottom-Left (Low Impact, Low Feasibility) — “Defer or Accept Risk”
Niche applications, EOL systems. Accept risk, plan decommission, or isolate only.
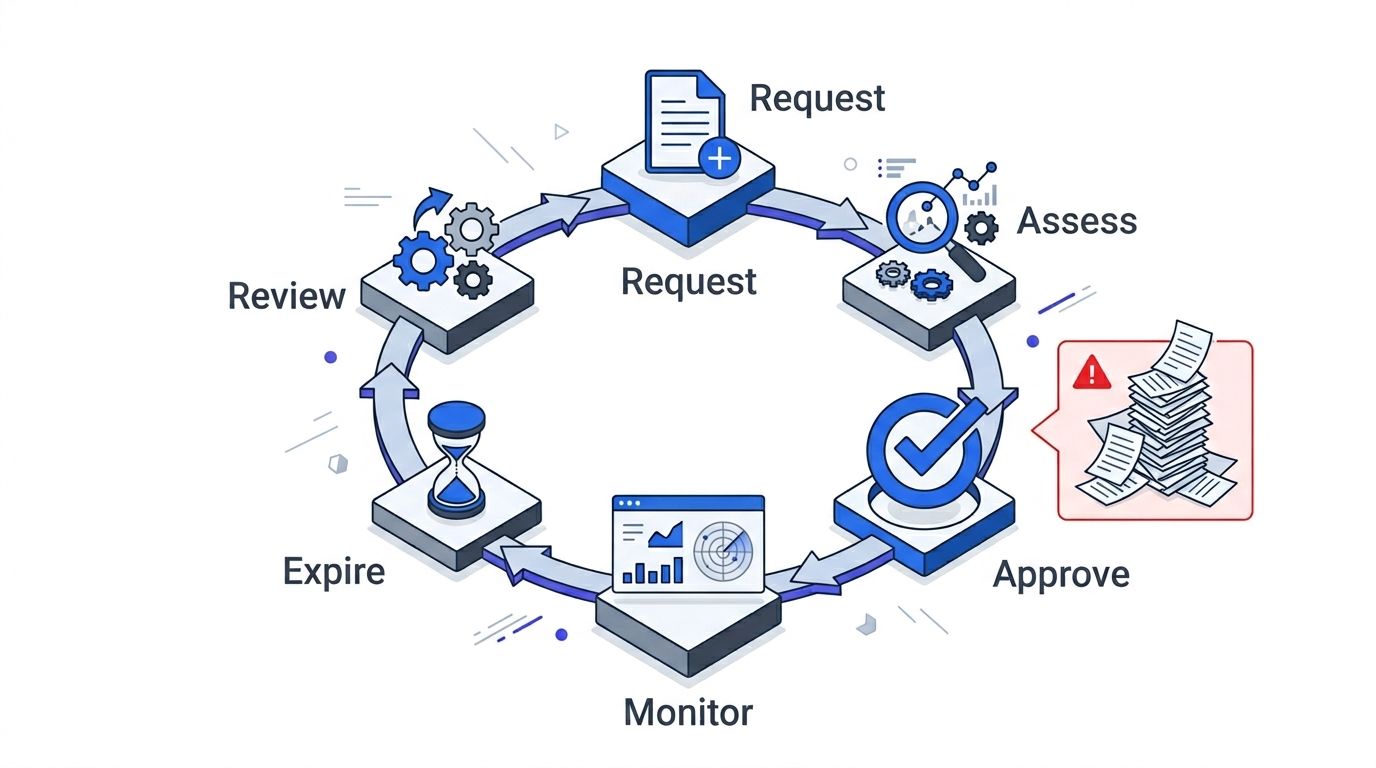
Governance & Inventory Process
Before you start scoring, establish one source of truth:
-
Assign an owner. One person (or small team) curates the application inventory. It lives in a spreadsheet, LeanIX, or ServiceNow.
-
Define scoring authority. For each app, involve:
- Application owner (business): rates Business Impact.
- Data governance / compliance: rates Data Sensitivity.
- IT / architecture: rates Technical Feasibility.
- Consensus call: If scores disagree, security lead breaks ties.
-
Lock the baseline. Once scored, the Tier 1 list becomes your Phase 1 commitment. Use this to justify budget, staffing, and timeline to the board.
-
Plan updates. Quarterly, re-score new applications (acquisitions, new SaaS). Existing scores rarely change.
Key Takeaways
Ruthless prioritization beats perfect planning. Your team will not secure 500 applications in 90 days. But it can secure 8–12 Tier 1 applications. That 10–15% often represents 85–90% of your business-critical data and revenue risk. Start there. Measure progress. Build momentum. Tier 2 and Tier 3 follow in predictable waves.
References & Further Reading
- NIST Cybersecurity Framework 2.0 — ID.AM-05: Assets are inventoried.
- LeanIX Application Criticality Matrix — Enterprise application assessment platform.
- AWS Prescriptive Guidance: Application Assessment — Free framework for scoring cloud readiness.
- Fluency: Zero Trust Maturity Model — Reference implementation timelines.
Internal Navigation
This article is part of the Zero Trust strategy series:
- Foundation (read first): Executive Guide to Zero Trust Architecture
- Phase 1 Hub: 90-Day Zero Trust Playbook (coming soon)
- Next step: Building Your Zero Trust Governance Structure (coming soon)
- Implementation: Baseline Metrics & Monitoring (coming soon)
Related topic: The prioritization in this scorecard directly drives your segmentation strategy — your highest-scoring applications become your first network zones.
About the Author
Sven Schuchardt is a platform engineering advisor and CTO strategist working with Fortune 500 companies on Zero Trust migration, supply chain security, and DevOps modernization. He publishes regularly on cybersecurity and application architecture topics.