Micro-Segmentation Design: Choosing Your Approach
Published
Most micro-segmentation failures are tool choices disguised as strategy decisions. Teams pick a vendor, then retrofit the environment around it. The result is a Kubernetes estate stuck with host-based agents it doesn’t need, or a VMware datacenter paying for a cloud-native SDN it can’t use. Gartner’s forecast that multi-strategy segmentation adoption rises from under 5% in 2023 to 25% by 2027 is really a signal that the single-vendor answer stops working past a certain scale.
This is Phase 2, Chapter 3 of the 90-Day Zero Trust Playbook. The design work happens in Phase 2. Enforcement is Phase 3. If you conflate them, you will either block production or quietly retreat to permissive mode and pretend segmentation is in place.
Key Takeaways
- Segmentation approach follows environment — K8s-native estates fit service mesh or eBPF; hybrid and legacy estates fit host-based agents (Gartner)
- Multi-strategy adoption rises from <5% (2023) to ~25% by 2027 — single-tool answers don’t survive hybrid reality (Gartner)
- Cost reality: cloud-native security groups are free; service mesh adds ~10–30% infrastructure overhead; host-based SDN runs $5,000+/month in subscription (Illumio pricing)
- Gradual, observation-first rollout cut segmentation-related outages by 40% vs. manual deployment in Illumio’s 2024 customer study (Illumio 2024)
- Even mature programmes only reach ~60% of apps segmented by count — the design question is which 60% matter most, not how to hit 100%
Design Before Enforcement
A clean way to separate the two: design is the document that says “web tier talks to app tier on port 443, app tier talks to DB tier on port 5432, nothing else.” Enforcement is the switch that blocks the traffic that isn’t on that list. Phase 2 produces the document. Phase 3 flips the switch — see Graduated Enforcement.
The input to the design document is the network baseline from Chapter P5 — the observed flows, not the architecture diagram. The output is policy grouped by what you’re protecting (application tier, data class), not by where it runs (subnet, VPC).
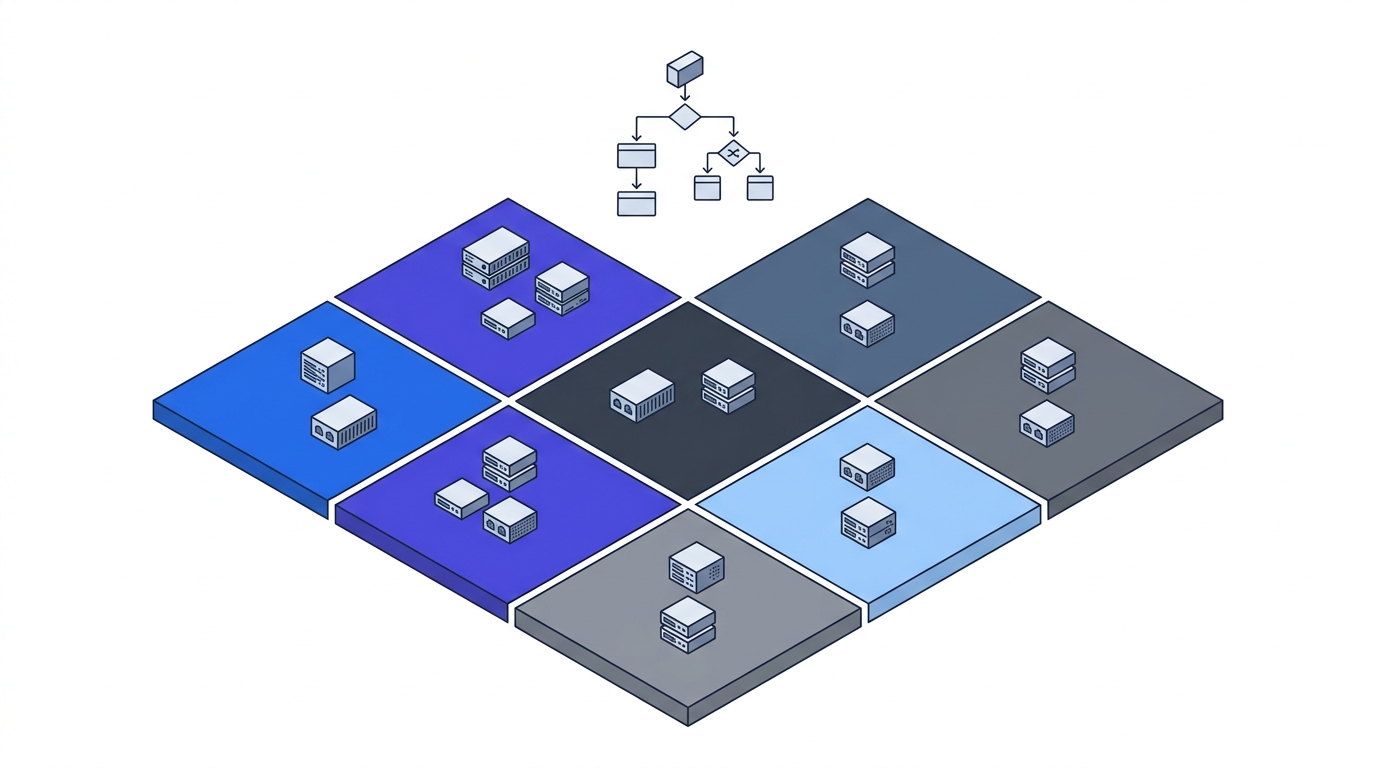
The Environment-First Decision Tree
Start from where your workloads actually run. Tool choice falls out of the answer.
Kubernetes-native. Service mesh (Istio, Linkerd) or eBPF-based CNI (Cilium). Mesh gives you identity-aware policy at L7 with mTLS by default; eBPF operates at kernel level with per-flow cost in the sub-millisecond range (Cilium benchmarks). For pure K8s, Cilium is the default choice; for multi-tenant or multi-cluster with strong policy requirements, Linkerd’s operational simplicity wins over Istio’s feature surface.
Cloud IaaS (AWS, Azure, GCP). Cloud-native security groups, NSGs, and firewall rules are free, granular, and already in place. Your baseline from Chapter P5 already shows the flows; translate them into group rules. Terraform or Pulumi makes the rules version-controlled. Don’t buy a third-party segmentation platform before exhausting what the cloud already gives you.
On-premises datacenter. VMware NSX if your hypervisor is VMware — ESXi-native, policy at the vNIC, and customer field data shows 75% faster lateral-movement response times — or host-based agents (Illumio, Guardicore) if the estate is mixed hypervisor. NSX is not portable off VMware; factor that into the decision if you’re mid-cloud-migration.
Hybrid (K8s + cloud + on-prem). Overlay approach. Cilium ClusterMesh, Consul service-to-service, or host-based agents that span environments. Expect higher integration cost and more operational discipline. This is where the Gartner 25%-by-2027 multi-strategy number comes from — hybrid forces plurality.
Legacy (mainframe, VLAN-bound, pre-virtualisation). VLAN + monitor, not segment. Isolation is the goal, not fine-grained policy. Put the legacy system on its own VLAN, log every flow into and out of it, and treat the boundary as a compensating control. Full segmentation is a modernisation project, not a 90-day play.
Vendor Snapshot (Not a Buying Guide)
Three reference points for the RFP, not an endorsement list:
- Illumio — Host-based, rated 4.8★ from 147 reviewers on Gartner Peer Insights. Strong in hybrid and brownfield. Subscription cost is real (four to five figures per month at mid-market scale).
- VMware NSX (now Broadcom/VCF) — Hypervisor-native for VMware estates. Field study reports 75% faster lateral movement response versus non-segmented baseline. Lock-in to VMware is the trade-off post-Broadcom acquisition.
- Cilium — Open-source, eBPF-based, de facto K8s standard. Sub-millisecond per-flow overhead, first-class in every major managed Kubernetes (EKS, AKS, GKE Dataplane V2). Commercial support via Isovalent for enterprise features.
The RFP-killer question for any vendor: show me a customer in my environment shape who went from observation to enforcement without a P1 incident. If they can’t, scope the POC around that exact transition.
The Cost Reality
Budget honestly, at least at three orders of magnitude:
- Free / in-the-bundle: Cloud security groups, NSGs, VPC firewall rules, Cilium Network Policies (with self-operated Cilium). Cost is labour, not licence.
- ~10–30% infra overhead: Service mesh sidecars (Istio, Linkerd) add CPU and memory per pod. Linkerd’s benchmarks show 40–400% lower latency and ~30% less memory than Istio — pick accordingly if the critical path is latency-sensitive.
- $5,000+/month subscription: Host-based (Illumio, Guardicore), enterprise NSX, commercial Cilium (Isovalent). Justified at scale; wasteful for a 500-node K8s estate that Cilium free-tier could segment.
The cost that overruns every programme is the labour of getting from design to enforcement — not the licence. Budget the people, not just the tool.
Observation-Before-Enforcement Is Non-Negotiable
Every mature platform supports an observation mode before blocking: Istio PERMISSIVE mTLS, Illumio Visualisation, NSX Idle, Cilium Audit. Use it. Illumio’s 2024 field data shows a 40% reduction in segmentation-related outages when programmes spent 30–90 days in observation before enforcement vs. manual cut-over.
During observation:
- Run the policy in log-only mode for 30 days minimum (90 for T0 systems).
- Review policy violations weekly. Each violation is either a mis-designed rule, a surprise dependency, or a real policy gap.
- Refine the policy. Ship to enforcement only after a two-week window with zero unexplained violations on T0/T1 flows.
The 40% outage reduction is the ROI number that pays for the 30–90 days of “delay.” It isn’t delay. It’s the programme.
The 60% Truth
Elisity and other vendor-neutral data put real-world segmentation coverage around 60% of apps by count, even in mature programmes. The remaining 40% are legacy systems, acquired estates, and the “we’ll get to it next year” backlog.
This is not a failure. It is the reason Application Criticality Scorecard matters so much: if the segmented 60% contains every T0 and T1 application, you have succeeded. If it contains the easy wins and leaves T0 unsegmented, you’ve optimized the wrong metric.
What You Hand to Phase 3
By the end of this chapter, you should have:
- A segmentation design document mapped to the Chapter P5 baseline — groups by application tier and data class, not by subnet
- Tool selection justified against environment shape, not vendor preference
- Policy running in observation mode on at least one T0 application group, with weekly violation review in place
- A 30–90 day observation window scheduled before Phase 3 enforcement begins
- A “which 60% matters most” prioritisation that puts every T0/T1 in-scope
Return to the 90-Day Playbook hub for Phase 3 and the cross-cutting operations chapters.


